Asahi Group Holdings Breach Investigation Reveals 1.9 Million Affected as Qilin Ransomware Dominates 2025 Attack Landscape

Bottom Line Up Front: Japanese beverage giant Asahi Group Holdings has concluded its two-month investigation into September's devastating ransomware attack, confirming that personal data of approximately 1.9 million individuals was potentially exposed in a Qilin ransomware operation that crippled production across 30 factories. The attack, which forced nationwide product shortages and manual order processing, highlights Qilin's emergence as 2025's most prolific ransomware group with over 105 confirmed attacks this year, powered by sophisticated bulletproof hosting infrastructure spanning Russia, Hong Kong, and sanctioned networks.
Investigation Findings: Two Months to Contain the Damage
On November 27, 2025, Asahi Group Holdings released the complete findings from its internal investigation into the ransomware attack that disrupted operations beginning September 29. The scope of the breach is significantly larger than initially feared:
Affected Individuals:
- 1.525 million customers who contacted Asahi via customer service centers
- 107,000 current and former employees
- 168,000 family members of staff
- 114,000 external contacts (business partners and recipients of corporate communications)
Total potential exposure: 1.914 million individuals
Notably, only 18 employee-related cases have been definitively confirmed as compromised, and Asahi emphasized that no credit card information was accessed. The exposed data primarily includes names, addresses, gender, phone numbers, and email addresses.
Attack Timeline: Four Hours Too Late
According to Asahi's forensic analysis, the attack unfolded with devastating speed on September 29, 2025:
7:00 AM JST: Systems at one of Asahi's data centers were disrupted; encrypted files discovered across the network
Within 4 hours: Network isolation and data center disconnection initiated
Too late: Attackers had already infiltrated through compromised equipment at a separate Asahi site, deploying ransomware across multiple servers and connected PCs
The forensic investigation revealed that threat actors had breached the network through compromised equipment at a separate facility before launching the ransomware payload, demonstrating the sophisticated lateral movement capabilities that make modern ransomware attacks so devastating.
Operational Chaos: From Digital to Manual
The attack forced Asahi into operational crisis mode across Japan:
- 30 factories temporarily unable to manage digital workflows
- Nationwide product shortages as retailers and restaurants reported out-of-stock Asahi beverages
- Manual order processing via phone, fax, and handwritten orders implemented to maintain supply
- 12 new product launches postponed due to system outages
- Full-year financial results delayed to focus on recovery efforts
Production at six beer factories gradually resumed using manual processes by early October, with the company spending nearly two months containing the attack, restoring systems, and rebuilding network infrastructure.
CEO Confirms No Ransom Negotiations
In his first public statement since the attack, CEO Atsushi Katsuki made a definitive stance clear at a November 27 news conference:
"We have not been in touch with the attacker. Even if we had a ransom demand, we would not have paid it."
Katsuki characterized the attack as "beyond our imagination" and "a sophisticated and cunning attack," despite the company believing it had taken "full and necessary measures" to prevent such incidents. The statement echoed growing concerns about Japan's escalating cybersecurity crisis, with multiple major Japanese corporations falling victim to ransomware and data extortion campaigns throughout 2025.
The CEO apologized to customers and partners while confirming that product shipments are gradually resuming as operational systems recover. Electronic ordering systems are scheduled to begin restoration in early December, with near-normal operations targeted by February 2026.

Qilin's Data Extortion: 27GB and a $10 Million Price Tag
On October 7, 2025, the Qilin ransomware group publicly claimed responsibility for the Asahi attack, listing the company on their "WikiLeaksV2" data leak site. The group alleged they had stolen 27GB of sensitive data, including:
- Financial documents and budgets
- Contracts and development forecasts
- Employee personal information and IDs
- Internal planning reports
Sample screenshots posted by Qilin substantiated their claims. According to Resecurity's HUNTER investigators, who engaged in private conversations with Qilin operators, the threat actors are attempting to sell the stolen Asahi data for $10 million USD on underground markets.
As of the investigation's conclusion, Asahi confirmed "no confirmed evidence that any stolen data has been publicly released online," though the potential for future exposure remains.
Qilin's Reign: 2025's Most Prolific Ransomware Operation
The Asahi attack represents just one victory in Qilin's unprecedented 2025 campaign. The Russian-speaking Ransomware-as-a-Service (RaaS) operation has emerged as the year's dominant threat actor:
2025 Attack Volume:
- 105+ confirmed attacks publicly acknowledged by victims
- 473 unconfirmed claims not yet verified
- Most active group for Q2 and Q3 2025 consecutively, as detailed in our August 2025 threat analysis
- October 2025: Over 50 new victims across 15 countries
For comparison, Qilin claimed 186 victims in all of 2024. The group has claimed more victims in the first six months of 2025 than several other top ransomware gangs combined.
Recent High-Profile Victims:
- Volkswagen Group France (October 2025)
- Spanish Tax Administration Agency (Agencia Tributaria, October 2025)
- 28 South Korean asset management firms (September 2025, "Korean Leaks" campaign)
- Multiple U.S. electric cooperatives including San Bernard and Karnes
- Globelink International (September 2025, 22GB exfiltrated)
- Habib Bank AG Zurich (November 2025, 2.5TB stolen)
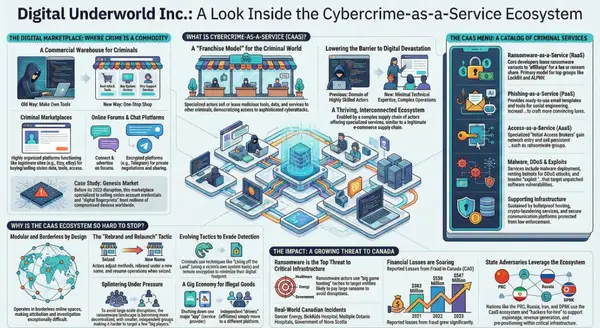
The Bulletproof Hosting Backbone
Recent investigations by Resecurity, published in October 2025, exposed the critical infrastructure enabling Qilin's global operations: a sophisticated network of bulletproof hosting (BPH) providers that operate with "minimal or no oversight" across jurisdictions designed to resist law enforcement.
The Ghost Network:
Qilin's infrastructure spans entities in Russia, Hong Kong, Cyprus, and the UAE, connected through a complex web of shell companies and sanctioned networks:
Key BPH Providers:
- Cat Technologies Co. Limited (Hong Kong)
- Chang Way Technologies (Hong Kong)
- Starcrecium Limited (Cyprus)
- Hostway.ru / OOO "Information Technologies" (Russia, St. Petersburg)
- Red Bytes LLC (Russia)
- BEARHOST Servers (aka Underground, Voodoo Servers)
These entities are linked through common directors, shared IP addresses, and overlapping business addresses. Corporate records reveal Lenar Davletshin serves as director of numerous interconnected hosting entities across multiple jurisdictions.
Sanctioned Infrastructure:
The U.S. Treasury Department sanctioned Aeza Group in July 2025 for providing bulletproof hosting services to cybercriminals, specifically supporting:
- Ransomware groups like BianLian
- Infostealers including Meduza and Lumma
- Dark web drug markets like BlackSprut
- Pro-Kremlin disinformation operations (Doppelgänger campaign)
Some Qilin infrastructure shows overlap with Aeza-linked networks, suggesting shared backend support systems. Following sanctions and abuse complaints, BEARHOST announced a transition to "private mode" in late December 2024, accepting new customers only through vetting and existing client referrals—a common pattern among underground vendors seeking to minimize law enforcement exposure, as detailed in our coverage of Operation Endgame's disruption of bulletproof hosting networks.
The RaaS Business Model: 80-85% Affiliate Commissions
Qilin operates a sophisticated Ransomware-as-a-Service platform that attracts top-tier affiliates through generous profit-sharing:
Platform Features:
- User-friendly web panel for attack configuration
- Victim management and ransom negotiation tools
- Data Leak Site (DLS) on Tor for publishing stolen information
- Ransomware variants written in Rust and Golang for cross-platform compatibility
Profit Distribution:
- Affiliates: 80-85% of ransom payments
- Operators: 15-20% commission
This generous split attracts experienced cybercriminals who execute the actual attacks while Qilin provides infrastructure, malware, and support.
State-Sponsored Convergence: North Korean Involvement
Microsoft's threat intelligence revealed a concerning development in February 2025: Moonstone Sleet, a North Korean state-sponsored threat actor, has been observed deploying Qilin ransomware at select organizations.
This represents the dangerous convergence of financially motivated cybercrime and state-sponsored operations, with nation-state actors potentially using RaaS platforms to generate revenue while maintaining plausible deniability.
The 2025 Ransomware Alliance: DragonForce, Qilin, and LockBit
In a development reminiscent of the 2020 Maze ransomware "cartel," Qilin has formed a coalition with two other notorious groups:
- DragonForce
- LockBit
This alliance enables resource sharing, infrastructure cooperation, and coordinated attacks. The coalition emerged in 2025, with DragonForce offering similarly generous 80%+ affiliate commissions, as documented in our analysis of global cybercrime takedowns and ransomware group evolution.
The collaboration model mirrors the historical Maze alliance that popularized double extortion tactics, where threat actors both encrypt and exfiltrate victim data to maximize pressure.
Asahi's Recovery and Enhanced Security Measures
Following the two-month containment and recovery effort, Asahi has implemented comprehensive security enhancements:
Technical Controls:
- Strengthened network communication controls and segmentation
- Upgraded threat-monitoring and detection systems
- New backup architectures with air-gapped storage
- Enhanced endpoint protection across manufacturing systems
Organizational Measures:
- More rigorous employee cybersecurity training programs
- Regular incident response exercises and tabletop drills
- External cybersecurity audits as standard practice
- Enhanced governance and oversight procedures
The company submitted its final investigation report to Japan's Personal Information Protection Commission on November 26, 2025.
Industry Expert Warnings: The Window is Shrinking
Chris Dimitriadis, Chief Global Strategy Officer at ISACA, emphasized the accelerating threat landscape:
"The window to detect and stop an attack is shrinking. Ransomware attacks are becoming faster and more sophisticated, with AI enhancing the speed and precision of criminal tactics."
Dimitriadis stressed the need for organizations to make proactive cybersecurity prevention and training core business priorities, with frequent incident-response exercises and a culture of shared digital responsibility.
Renata Naurzalieva, director of Japan operations at business development consultancy Intralink, noted cultural challenges:
"Japan has always been a little bit complacent in terms of cybersecurity. A lot of Japanese companies, when they think about investment in cybersecurity, they still try to justify the return on investment. But it's not the return on investment that you're looking for, it's 'can it protect my assets, can it protect my network data?'"
A survey released in June 2025 found that one-third of Japanese businesses had experienced cyberattacks of some sort, underscoring the growing threat landscape facing the region.
Japan's Cybersecurity Crisis: A Pattern of Escalating Attacks
The Asahi breach is part of an alarming surge in cyberattacks targeting Japanese corporations throughout 2025. October alone witnessed multiple devastating incidents that disrupted critical supply chains and exposed millions of records:

Askul Corporation Ransomware Attack (October 2025): The retail giant fell victim to RansomHouse, with attackers claiming to have stolen 1.1 terabytes of data. The breach forced suspension of three major e-commerce platforms (Askul, Lohaco, and Soloel Arena) and created cascading supply chain disruptions affecting Muji and The Loft retail operations.
Nikkei Inc. Slack Breach (September 2025): Japan's media giant and Financial Times owner suffered a sophisticated infostealer attack that compromised 17,368 employee and business partner accounts through infected personal computers accessing corporate Slack workspaces.
TEIN Auto Parts: The manufacturer experienced ransomware that crippled its headquarters network, halting operations across affiliated firms.
Sagawa Express: One of Japan's largest transportation companies reported unauthorized account logins traced to compromised credentials.
This concentration of attacks suggests Japanese corporations are increasingly becoming priority targets for organized cybercrime groups, possibly due to perceived vulnerabilities in legacy cybersecurity infrastructure, delayed adoption of modern security practices, and the high-value nature of Japanese manufacturing and technology companies.
Broader Manufacturing Sector Targeting
The Asahi attack is part of Qilin's systematic targeting of manufacturing operations, a trend documented in our comprehensive analysis of major cyber attacks in 2025. In 2025, the group has claimed:
- 14 confirmed attacks against manufacturers
- 138 total ransomware attacks on manufacturers industry-wide (all groups)
Manufacturing represents an attractive target due to:
- Just-in-time production models with low tolerance for disruption
- Complex supply chain dependencies
- Often outdated operational technology (OT) systems
- High costs associated with production downtime
The attack bears striking similarities to Trinity of Chaos's ransomware attack on Jaguar Land Rover (JLR), which:
- Halted production at all major plants globally (UK, Slovakia, Brazil, India)
- Completely stopped vehicle assembly lines
- Led to estimated losses approaching £72 million ($97 million) per day
Asahi faced the prospect of an 83% drop in domestic operating profit if the outage had persisted beyond early recovery efforts.
Technical Analysis: Sophisticated Lateral Movement
While Asahi has not disclosed the specific initial access vector, the attack demonstrates several sophisticated techniques:
Likely Initial Access Methods (based on sector trends):
- Phishing emails with malicious attachments or links
- Exploitation of public-facing application vulnerabilities
- Compromised valid accounts through credential theft
- Supply chain compromise through third-party access
Attack Progression:
- Initial compromise of equipment at separate Asahi facility
- Lateral movement across network to primary data center
- Deployment of ransomware across multiple servers and endpoints
- Data exfiltration of 27GB before encryption
- Encryption and production of ransom note
The attack demonstrates Qilin affiliates' ability to:
- Establish persistent access across multiple sites
- Move laterally without detection
- Exfiltrate significant data volumes
- Coordinate multi-site encryption for maximum impact
The Double Extortion Playbook
Qilin's attack on Asahi followed their standard double extortion methodology:
Phase 1: Network Infiltration
- Gain initial access through compromised credentials or vulnerabilities
- Establish persistence and deploy reconnaissance tools
- Map network architecture and identify high-value targets
Phase 2: Data Exfiltration
- Identify and compress sensitive data
- Exfiltrate to attacker-controlled infrastructure
- Verify data integrity and value for extortion
Phase 3: Ransomware Deployment
- Deploy ransomware across maximum number of systems
- Encrypt critical operational and business data
- Drop ransom notes with contact information
Phase 4: Extortion
- List victim on data leak site as pressure tactic
- Threaten public release if ransom not paid
- Stage sample data releases to demonstrate access
- Escalate pressure through increasing data dumps
This approach significantly increases pressure on victims, who face not only operational disruption but also regulatory penalties, reputational damage, and potential legal liability from exposed data.
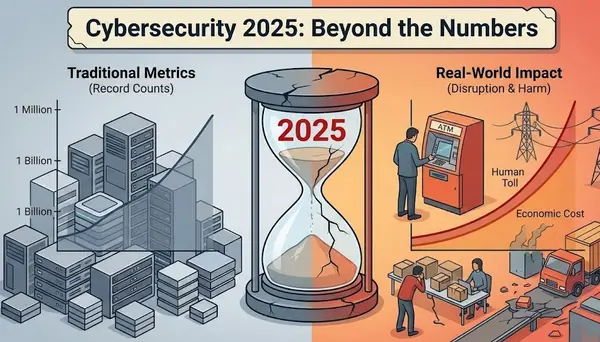
Global Impact: 2025 Ransomware Statistics
The Asahi attack occurs within a broader context of escalating ransomware activity:
2025 Year-to-Date:
- 4,441+ organizations publicly listed as ransomware victims
- ~51% estimated payment rate, resulting in approximately 2,268 ransom payments
- $1 million median ransom payment per breach
- Qilin-specific demands: $200,000 to $4 million range
Quarterly Trends (Q3 2025):
- 1,429 extortion incidents (5% increase from Q2)
- Down one-third from record Q1 2025 (1,961 incidents), as documented in our comprehensive 2025 cybersecurity landscape briefing
Some experts predict ransomware damage costs could exceed $265 billion by 2031.
Recommendations for Organizations
Based on the Asahi incident and broader threat landscape, security experts recommend:
Immediate Actions:
- Network Segmentation: Isolate critical production systems from IT networks
- Multi-Factor Authentication: Implement MFA across all remote access points
- Backup Verification: Test restoration procedures; maintain air-gapped backups
- Vulnerability Management: Prioritize patching of public-facing applications
- Third-Party Risk: Assess security posture of all vendors with network access
Strategic Investments:
- Threat Detection: Deploy EDR/XDR solutions with behavioral analytics
- Incident Response: Establish and regularly test IR plans and runbooks
- Security Training: Conduct regular phishing simulations and awareness training
- Cyber Insurance: Review coverage for ransomware and business interruption
- External Audits: Engage independent security assessments annually
Cultural Shifts:
- Executive Buy-In: Treat cybersecurity as business risk, not IT problem
- Response Exercises: Conduct tabletop exercises involving leadership
- Information Sharing: Participate in industry ISACs and threat intelligence sharing
- No-Ransom Policy: Establish clear policy against ransom payments
- Regulatory Compliance: Ensure breach notification procedures meet all jurisdictions
Conclusion: A Wake-Up Call for Critical Infrastructure
The Asahi Group Holdings ransomware attack represents a critical inflection point in understanding modern ransomware threats. With 1.9 million individuals potentially affected, two months to recover operations, nationwide product shortages, and estimated losses potentially reaching hundreds of millions of dollars, the incident demonstrates the catastrophic impact of sophisticated ransomware operations.
Qilin's emergence as 2025's dominant ransomware group, powered by bulletproof hosting infrastructure that spans sanctioned Russian networks and Hong Kong shell companies, reveals the inadequacy of current defensive measures and the challenges facing international law enforcement.
For organizations across manufacturing, critical infrastructure, and beyond, the message is clear: the window to detect and respond to attacks is shrinking, the sophistication of adversaries is increasing, and the cost of inadequate cybersecurity preparation has never been higher.
As Asahi works toward full operational recovery by February 2026, the incident serves as a stark reminder that in the modern threat landscape, it's not a question of if an organization will be targeted, but when—and whether they'll be prepared to respond effectively.
Related Coverage:
- Habib Bank AG Zurich Hit by Qilin Ransomware: 2.5TB of Sensitive Data Stolen in Major Banking Breach
- Ransomware Onslaught: Multiple Groups Post Fresh Victims on October 3, 2025
- August 2025: A Month of Unprecedented Cyber Attacks and Data Breaches
Sources: Asahi Group Holdings official statements, Comparitech, Resecurity HUNTER, Bloomberg, AFP, Infosecurity Magazine, CyberInsider, Cybernews, TechRepublic, ISACA, Microsoft Threat Intelligence, U.S. Department of Treasury, Ransomware.live
Published: November 28, 2025 Last Updated: November 28, 2025 Author: Security Research Team Category: Ransomware, Data Breach, Manufacturing Tags: Qilin, Asahi Group Holdings, RaaS, Bulletproof Hosting, Japan Cybersecurity, Double Extortion, Manufacturing Security