Rethinking How We Measure Cyber Catastrophe
Published in partnership with *CISO Marketplace *| January 2026
Executive Summary
The year 2025 will be remembered as a watershed moment in cybersecurity history. Traditional metrics of breach severity—record counts in the millions, even billions—tell only part of the story. The most consequential attacks this year revealed a troubling truth: counting compromised records is an inadequate measure of real-world impact.
This report examines 2025’s most significant cyber incidents through two critical lenses: the traditional data-centric view and an emerging disruption-and-harm framework that captures the true human and economic toll of modern cyberattacks. What emerges is a compelling case for fundamentally rethinking how organizations, regulators, and the public measure cybersecurity catastrophe.
Part One: The Data-Centric View
Top 10 Breaches by Records Compromised
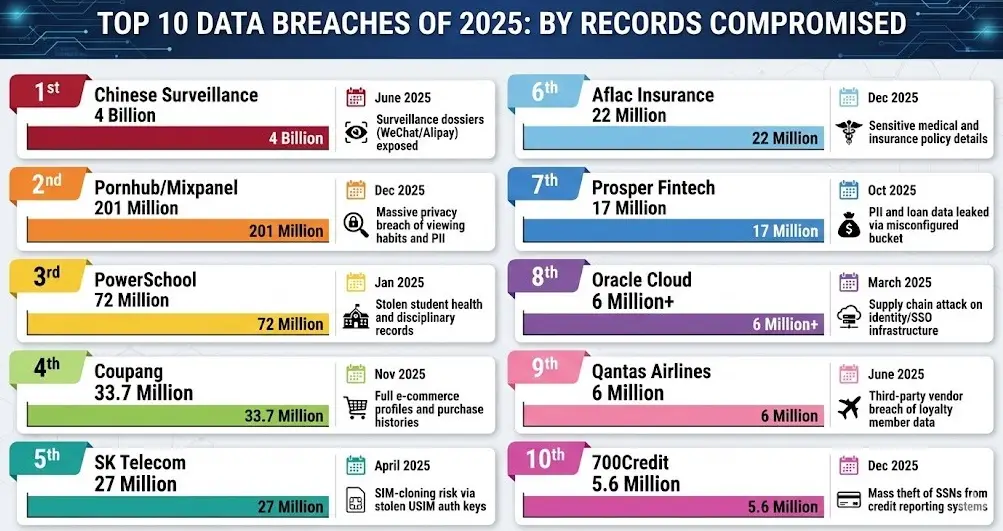
By conventional metrics, 2025 produced unprecedented breach volumes:
Date Entity Records Impact
June 2025 Chinese Surveillance 4 Billion Surveillance dossiers (WeChat/Alipay) exposed
Dec 2025 Pornhub/Mixpanel 201 Million Massive privacy breach of viewing habits and PII
Jan 2025 PowerSchool 72 Million Stolen student health and disciplinary records
Nov 2025 Coupang 33.7 Million Full e-commerce profiles and purchase histories
April 2025 SK Telecom 27 Million SIM-cloning risk via stolen USIM auth keys
Dec 2025 Aflac Insurance 22 Million Sensitive medical and insurance policy details
Oct 2025 Prosper Fintech 17 Million PII and loan data leaked via misconfigured bucket
March 2025 Oracle Cloud 6 Million+ Supply chain attack on identity/SSO infrastructure
June 2025 Qantas Airlines 6 Million Third-party vendor breach of loyalty member data
Dec 2025 700Credit 5.6 Million Mass theft of SSNs from credit reporting systems
The Chinese Surveillance Mega-Leak: 4 Billion Records
In June 2025, cybersecurity researcher Bob Dyachenko and the Cybernews research team discovered what may be the largest single-source leak of Chinese personal data ever identified. A 631-gigabyte database containing approximately 4 billion records was found sitting on an unprotected server without password authentication.
- 805+ million WeChat records (IDs, metadata, potentially communication logs)
- 780 million residential addresses with geographic identifiers
- 630 million financial records including payment card numbers, dates of birth, names, and phone numbers
- 300 million Alipay card and token records
- Additional collections covering vehicle registrations, pension funds, employment records, gambling data, and insurance information
Researchers characterized the database as “a centralized aggregation point, potentially maintained for surveillance, profiling, or data enrichment purposes.” The dataset appeared meticulously assembled to build comprehensive behavioral, economic, and social profiles of Chinese citizens.
The database’s rapid removal after discovery prevented attribution, but the sophistication suggests either state-level actors or highly organized cybercriminal operations. Security analysts noted this data could enable everything from large-scale phishing and blackmail to state-sponsored intelligence gathering and disinformation campaigns.
PowerSchool: 72 Million Students and Educators Exposed
The December 2024 breach of PowerSchool, publicly disclosed in January 2025, exposed data belonging to approximately 62 million students and 9.5 million educators across more than 18,000 schools globally. PowerSchool serves roughly 75% of the K-12 education market in North America.
US State Breach Notification Requirements TrackerComprehensive tool for researching breach notification laws, ransomware requirements, and privacy regulations across all 50 US states.![]() Breach Notification TrackerBreach Notification Tracker
Beyond Demographics—Sensitive Data Exposed:
Breach Notification TrackerBreach Notification Tracker
Beyond Demographics—Sensitive Data Exposed:
The breach went far beyond standard contact information. Investigations revealed:
- Special education status (IEP and 504 designations)
- Mental health conditions and therapy records
- Disciplinary records and behavioral notes
- Parental restraining orders and custody arrangements
- Medical alerts including anxiety disorders, medications, and health conditions
- Social Security numbers (for approximately 25% of affected students)
Root Cause Analysis:
The breach stemmed from fundamental security failures:
- No multi-factor authentication on PowerSchool’s customer support portal (PowerSource)
- Compromised employee credentials provided initial access
- Nine days of undetected access before PowerSchool discovered the breach
- PowerSchool only learned of the intrusion when the attacker contacted them to demand ransom
CrowdStrike’s forensic investigation revealed systematic failures in basic security controls. PowerSchool subsequently paid the ransom and received video purportedly showing data deletion—though security experts universally caution against trusting such assurances.
The Children’s Data Problem:
This breach highlights unique concerns around children’s data. Unlike adults, children cannot easily change their Social Security numbers or establish credit monitoring. Identity theft targeting minors often goes undetected for years, only surfacing when victims apply for student loans, jobs, or apartments.
SK Telecom: Three Years of Undetected Compromise
South Korea’s largest mobile carrier discovered in April 2025 that malware had been resident in its systems since June 2022—nearly three years of undetected compromise. The breach exposed approximately 27 million USIM records, representing effectively the carrier’s entire subscriber base.
Technical Analysis:
Attackers deployed sophisticated BPFDoor malware variants across at least 28 servers. BPFDoor exploits the Berkeley Packet Filter feature in Linux systems, allowing attackers to bypass traditional security mechanisms and remain undetected for extended periods.
Data Compromised:
- 26.95 million International Mobile Subscriber Identity (IMSI) records
- USIM authentication keys (Ki values)
- 290,000 International Mobile Equipment Identity (IMEI) records
- Network usage data
- SMS and contacts stored on SIMs
SIM-Cloning Risk:
The combination of IMSI, authentication keys, and IMEI data creates significant SIM-cloning risks. While SK Telecom and regulators downplayed this possibility, the exposure of unencrypted authentication keys for 26+ million subscribers represents a fundamental breach of mobile security infrastructure.
Regulatory Response:
Korea’s Personal Information Protection Commission fined SK Telecom approximately $97 million, noting:
- Failure to implement basic access controls between internet-facing and internal systems
- 26+ million USIM authentication keys stored unencrypted
- Delayed breach notification (exceeding the 24-hour legal requirement)
- Security posture “very vulnerable to illegal intrusion”
The CEO publicly acknowledged this as “the worst hacking case in telecom history” for the company.
Oracle Cloud: Supply Chain Attack at Scale
In March 2025, a threat actor operating as “rose87168” claimed to have exfiltrated 6 million records from Oracle Cloud’s SSO and LDAP systems, potentially affecting over 140,000 enterprise tenants.
Initial Denial, Subsequent Confirmation:
Oracle initially denied any breach occurred. However, independent security researchers at CloudSEK verified:
- The compromised endpoint (login.us2.oraclecloud.com) was a legitimate production SSO endpoint
- Sample data shared by the attacker was confirmed valid by multiple affected companies
- The vulnerable server was running Oracle Fusion Middleware 11G software from 2014
Attack Vector:
The breach reportedly exploited CVE-2021-35587, a critical vulnerability in Oracle Access Manager that was added to CISA’s Known Exploited Vulnerabilities catalog in December 2022—yet remained unpatched on Oracle’s legacy servers.
Data Exposed:
- Encrypted SSO and LDAP passwords
- Java KeyStore (JKS) files
- Enterprise Manager JPS keys
- Personal emails associated with SSO credentials
Supply Chain Implications:
Security researchers characterized this as potentially “2025’s SolarWinds moment”—an attack on the supply chain layer where organizations mistakenly assume security is the cloud provider’s responsibility.
The exposure of JKS and key files creates risks of lateral movement across interconnected enterprise systems, potentially affecting organizations far beyond Oracle’s direct customer base.
Part Two: Beyond Record Counts—The Disruption Framework
The Fundamental Problem with Data-Centric Metrics
Traditional breach metrics focus on data volume: records compromised, gigabytes stolen, accounts exposed. But this framework misses the most important question: What harm was actually caused?
Consider:
- A breach exposing 1 million email addresses causes minimal harm
- A breach exposing 1,000 medical records with HIV status causes significant harm
- A breach disrupting hospital operations for weeks—even with no data theft—can cause deaths
A more complete picture emerges when we measure breaches by their:
- Operational disruption (services unavailable, processes halted)
- Human impact (injuries, deaths, psychological harm)
- Economic damage (direct costs, market value, GDP impact)
- Cascading effects (supply chain disruption, infrastructure dependencies)
By these metrics, several 2025 incidents stand out as potentially more consequential than their record counts suggest.
NHS Synnovis Attack: The First Confirmed Ransomware Fatality
On June 3, 2024, Russian ransomware group Qilin attacked Synnovis, a pathology services provider supporting NHS hospitals across southeast London. The attack’s full human toll became clear throughout 2025, culminating in the UK’s first officially confirmed ransomware-related death.
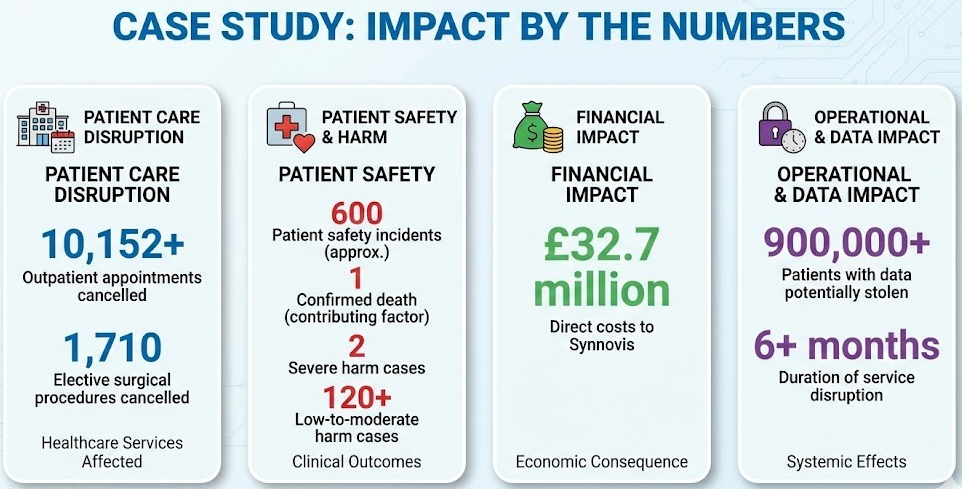
Impact by the Numbers
Metric Impact
Outpatient appointments cancelled 10,152+
Elective surgical procedures cancelled 1,710
Patient safety incidents ~600
Confirmed deaths (contributing factor) 1
Severe harm cases 2
Low-to-moderate harm cases 120+
Direct costs to Synnovis £32.7 million
Patients with data potentially stolen 900,000+
Duration of service disruption 6+ months
The Death That Changed Everything
In June 2025, King’s College Hospital NHS Foundation Trust confirmed that a patient “died unexpectedly” during the cyberattack. The subsequent patient safety investigation identified multiple contributing factors, prominently including “a long wait for a blood test result due to the cyber-attack impacting pathology services.”
Synnovis CEO Mark Dollar responded: “We are deeply saddened to hear that last year’s criminal cyber attack has been identified as one of the contributing factors that led to this patient’s death.”
This represents a categorical shift in how we must evaluate cyber incidents. A death cannot be measured in records. The Synnovis attack exposed roughly 900,000 patient records—a fraction of PowerSchool’s 72 million—yet its impact on human welfare was fundamentally different.
Beyond the Headlines: The Hidden Disruption
The official statistics understate the true disruption:
- Blood supply shortages persisted for months after the attack, affecting hospitals nationwide
- Primary care (GP practices) lost access to diagnostic services
- Cancer diagnoses were delayed as pathology services ground to a halt
- Emergency procedures proceeded without complete diagnostic information
- Healthcare workers operated in crisis mode for over six months
The attack prompted calls for a public inquiry into NHS cybersecurity and patient safety, with security expert Saif Abed urging NHS leaders to write to MPs requesting investigation.
Marks & Spencer: £300 Million and 46 Days of Chaos
In April 2025, ransomware group Scattered Spider brought one of Britain’s most iconic retailers to its knees through a sophisticated supply chain attack. The M&S incident demonstrated how modern cyberattacks can cascade into real-world disruption affecting millions of consumers.

Impact by the Numbers
Metric Impact
Lost operating profit £300 million (~30% of annual profits)
Market capitalization wiped out £750+ million
Days without online ordering 46 consecutive days
Employees affected 65,000
Stores impacted 1,400+
Recovery timeline Disruption continued through July 2025
The Attack Chain
The attack didn’t breach M&S directly. Instead, attackers:
- Targeted a third-party supplier with access to M&S systems
- Used social engineering to manipulate IT helpdesk staff into resetting passwords
- Gained access through “innocent insiders” who unknowingly provided credentials
- Deployed ransomware that encrypted systems and exfiltrated data
- Demanded ransom under classic double-extortion tactics
Real-World Consequences
The digital attack produced decidedly physical consequences:
- Food halls ran low as automated stock systems went offline
- Workers manually tracked inventory using pen and paper
- Staff physically checked refrigerator temperatures without digital monitoring
- Gift card terminals, returns kiosks, and loyalty services remained offline for weeks
- Fresh food and clothing supply chains were severely disrupted
CEO Stuart Machin described the incident as “a bump in the road,” but the company’s statement revealed deeper concerns: “We will use this window of disruption to accelerate our technology transformation plans; the plans we laid out a year ago. In fact, we will condense the two-year plan into just six months.”
The Supply Chain Dimension
The M&S attack coincided with similar incidents at Co-op and Harrods, suggesting coordinated targeting of British retail. The UK’s National Cyber Security Centre issued emergency guidance to retailers, warning of attackers exploiting IT helpdesk password reset procedures.
Jaguar Land Rover: Britain’s Most Expensive Cyberattack
On August 31, 2025, hackers struck Jaguar Land Rover in what the Cyber Monitoring Centre classified as the most financially damaging cyber event in British history. The attack demonstrates how modern manufacturing’s digital dependencies create catastrophic vulnerabilities.
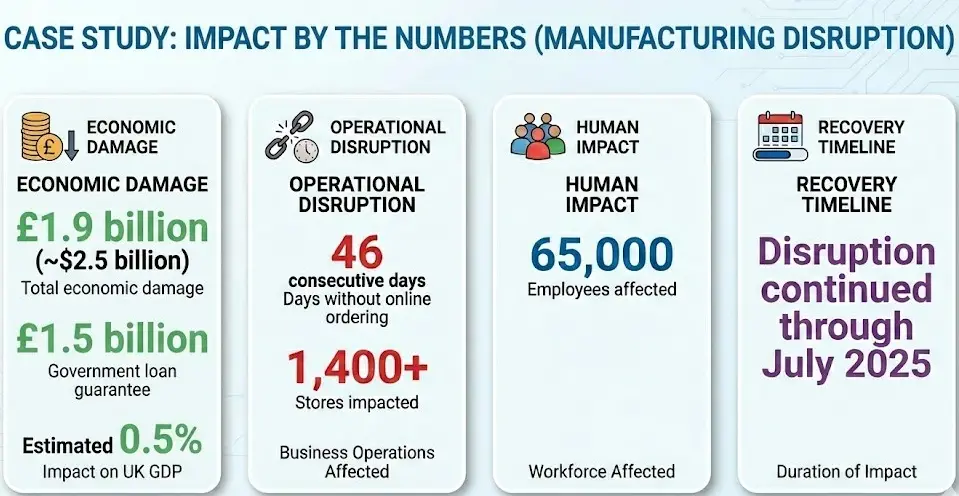
Impact by the Numbers
Metric Impact
Total economic damage £1.9 billion (~$2.5 billion)
Production shutdown duration 5+ weeks
Weekly losses £50+ million
Direct employees affected 33,000
Supply chain jobs at risk 104,000+
Businesses directly affected 5,000+
UK car production decline (September) 27%
Government loan guarantee £1.5 billion
Impact on UK GDP Estimated 0.5%
The Cascade Effect
JLR sits atop the UK’s largest automotive supply chain. The company directly employs 33,000 workers while supporting an estimated 120,000 to 200,000 additional jobs across hundreds of supplier companies. Many suppliers—small and medium-sized enterprises—depend heavily on JLR orders for survival.
When production stopped, the cascade was immediate:
- Just-in-time manufacturing meant suppliers had no buffer inventory
- Smaller suppliers began layoffs within days
- One supplier confirmed laying off 40 people—nearly half its workforce
- Trade union Unite reported supply chain workers being told to apply for Universal Credit
- Nearly 8 in 10 businesses in the West Midlands reported negative impacts
- 14% of affected businesses made redundancies by late September
MP Liam Byrne, Chair of the Commons Business and Trade Committee, described it as “a digital siege” and “a cyber shockwave ripping through our industrial heartlands.”
Unprecedented Government Intervention
The severity prompted extraordinary government action:
- UK Export Finance backed a £1.5 billion emergency loan to JLR
- This marked the first time the UK government provided direct financial support to a company specifically due to a cyberattack
- Business Secretary Peter Kyle called it “not only an assault on an iconic British brand but on our world-leading automotive sector and the men and women whose livelihoods depend on it”
The Insurance Gap
Reports indicate JLR had no active cyber insurance at the time of the attack. Unlike M&S, which expects to recover much of its £300 million loss through insurance, JLR must bear the full financial burden—explaining the necessity of government intervention.
Attribution and Method
The attack has been linked to Scattered Lapsus$ Hunters, a group connected to the Scattered Spider cybercriminals who targeted M&S and Co-op. JLR had actually suffered a prior breach in March 2025 when the HELLCAT ransomware group leaked hundreds of gigabytes of internal data using stolen credentials from 2021 that remained valid in 2025.
This earlier breach exposed development logs, source code, and cloud service credentials—potentially creating backdoors exploited in the September attack. The fact that four-year-old credentials still provided access highlights fundamental failures in credential lifecycle management.
Part Three: A New Framework for Measuring Cyber Impact
The ESG Dimension
The commenter who sparked this analysis identified a crucial insight: major cyberattacks are not merely information security events—they are ESG (Environmental, Social, and Governance) and HSE (Health, Safety, and Environment) issues.
Consider:
Traditional View ESG/HSE Reality
“900,000 records stolen” 1 death, 600 patient safety incidents
“Systems offline for 46 days” Food supply chain disruption, empty shelves
“Production halted for 5 weeks” 104,000 supply chain jobs at risk
“£300M in lost profit” £1.9B economic impact, 0.5% GDP effect
Proposed Impact Metrics
We propose evaluating cyber incidents across five dimensions:
1. Human Safety Impact
- Deaths (direct or contributing factor)
- Injuries and health consequences
- Delayed medical care
- Psychological harm
2. Operational Disruption
- Duration of service unavailability
- Percentage of operations affected
- Recovery timeline
- Manual workaround requirements
3. Economic Impact
- Direct costs (response, recovery, ransom)
- Lost revenue/profit
- Market value impact
- Insurance implications
- GDP-level effects
4. Supply Chain Cascade
- Number of dependent businesses affected
- Jobs at risk or lost
- Downstream service disruptions
- Critical infrastructure dependencies
5. Societal Impact
- Public services affected
- Consumer harm
- Community disruption
- National security implications
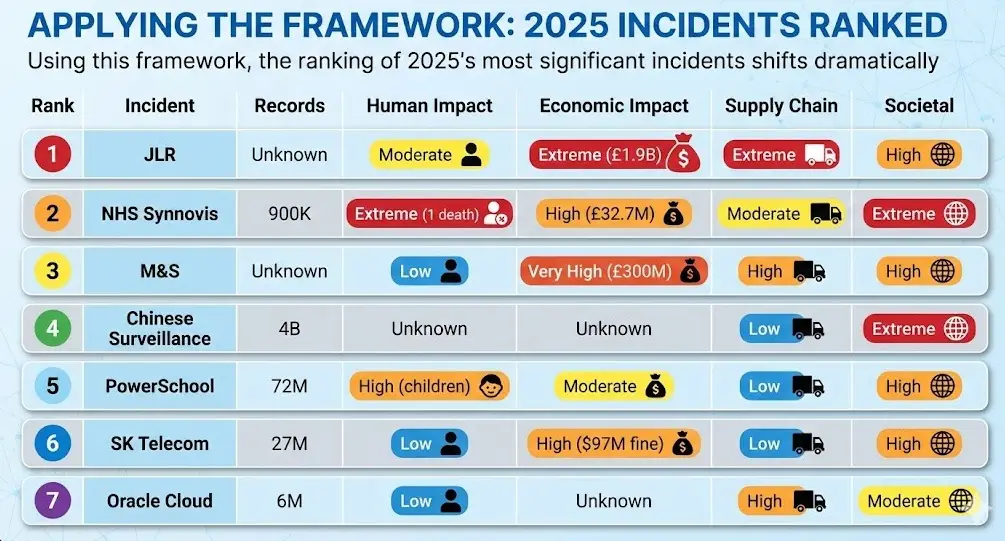
Applying the Framework: 2025 Incidents Ranked
Using this framework, the ranking of 2025’s most significant incidents shifts dramatically:
Rank Incident Records Human Impact Economic Impact Supply Chain Societal
1 JLR Unknown Moderate Extreme (£1.9B) Extreme High
2 NHS Synnovis 900K Extreme (1 death) High (£32.7M) Moderate Extreme
3 M&S Unknown Low Very High (£300M) High High
4 Chinese Surveillance 4B Unknown Unknown Low Extreme
5 PowerSchool 72M High (children) Moderate Low High
6 SK Telecom 27M Low High ($97M fine) Low High
7 Oracle Cloud 6M Low Unknown High Moderate
Part Four: Lessons and Implications
For Organizations
1. Cyber Risk Is Business Risk The JLR incident proves that cyber events can threaten corporate survival. A month of production downtime, compounded by supply chain dependencies, generated losses exceeding 50% of annual net profit.
2. Insurance Is Not Optional JLR’s lack of cyber insurance at the time of attack required unprecedented government intervention. Organizations must treat cyber insurance as essential risk transfer, not optional coverage.
3. Third-Party Risk Is First-Party Risk Both M&S and JLR were compromised through supply chain vulnerabilities. The security of your ecosystem partners is inseparable from your own security posture.
4. Credential Hygiene Prevents Catastrophe JLR was breached using credentials from 2021. SK Telecom stored authentication keys unencrypted. PowerSchool lacked MFA on critical portals. Basic security hygiene would have prevented or significantly limited each of these incidents.
For Regulators and Policymakers
1. Reporting Requirements Need Expansion Current breach notification frameworks focus on data exposure. Regulators should require reporting of operational disruption, human harm, and supply chain effects.
2. Critical Infrastructure Definitions Need Updating The JLR attack demonstrated that major manufacturers can be critical infrastructure through employment and economic effects. A single company’s shutdown affecting 0.5% of GDP warrants infrastructure-level protections.
3. Public Inquiry May Be Warranted The NHS Synnovis attack—resulting in confirmed death—demands systematic review. Security experts have called for public inquiry into NHS cybersecurity and patient safety.
For the Security Community
1. Develop Impact-Based Metrics The industry needs standardized frameworks for measuring disruption, harm, and cascade effects—not just record counts.
2. Study Real-World Consequences Security research focuses heavily on technical attack analysis. Equal attention should go to documenting human, economic, and societal consequences.
3. Communicate in Business Terms Security professionals must translate cyber risk into language executives and boards understand: jobs, revenue, market value, and human safety.
Conclusion: The Year Everything Changed
2025 will be remembered as the year cyberattacks definitively crossed from theoretical risk to documented catastrophe. A patient died. A billion pounds evaporated. Supply chain workers applied for welfare benefits. The UK government backstopped a private company’s cyber losses for the first time in history.
UK Government Admits Systemic Cybersecurity Failure After Years of Devastating BreachesA rare moment of transparency reveals decades of neglect, leaving critical infrastructure vulnerable to increasingly sophisticated attacks The Admission No One Expected In an unusually candid moment this week, the British government did something rare in the world of cybersecurity policy: it admitted complete failure. The Department for Science, Innovation![]() Breached CompanyBreached Company
Breached CompanyBreached Company
As we enter 2026, organizations, regulators, and the security community must embrace a more comprehensive framework for understanding cyber risk—one that accounts for the full spectrum of consequences when digital systems fail.
The breaches of 2025 prove that cybersecurity is no longer an IT problem. It is a human safety problem. An economic stability problem. A national security problem. Our metrics and responses must evolve accordingly.
About This Report
This analysis was prepared by CISO Marketplace, synthesizing research from:
- Cybernews, CloudSEK, SpyCloud (breach research)
- NHS England, King’s College Hospital NHS Foundation Trust (Synnovis impact)
- Cyber Monitoring Centre, SMMT, Unite (JLR analysis)
- Korea Personal Information Protection Commission (SK Telecom findings)
- Multiple news sources including BBC, Bloomberg, CNBC, The Record, and specialized security publications
For questions or additional analysis, contact the CISO Marketplace research team.
Document Version: 1.0 Last Updated: January 2026 Classification: Public Distribution