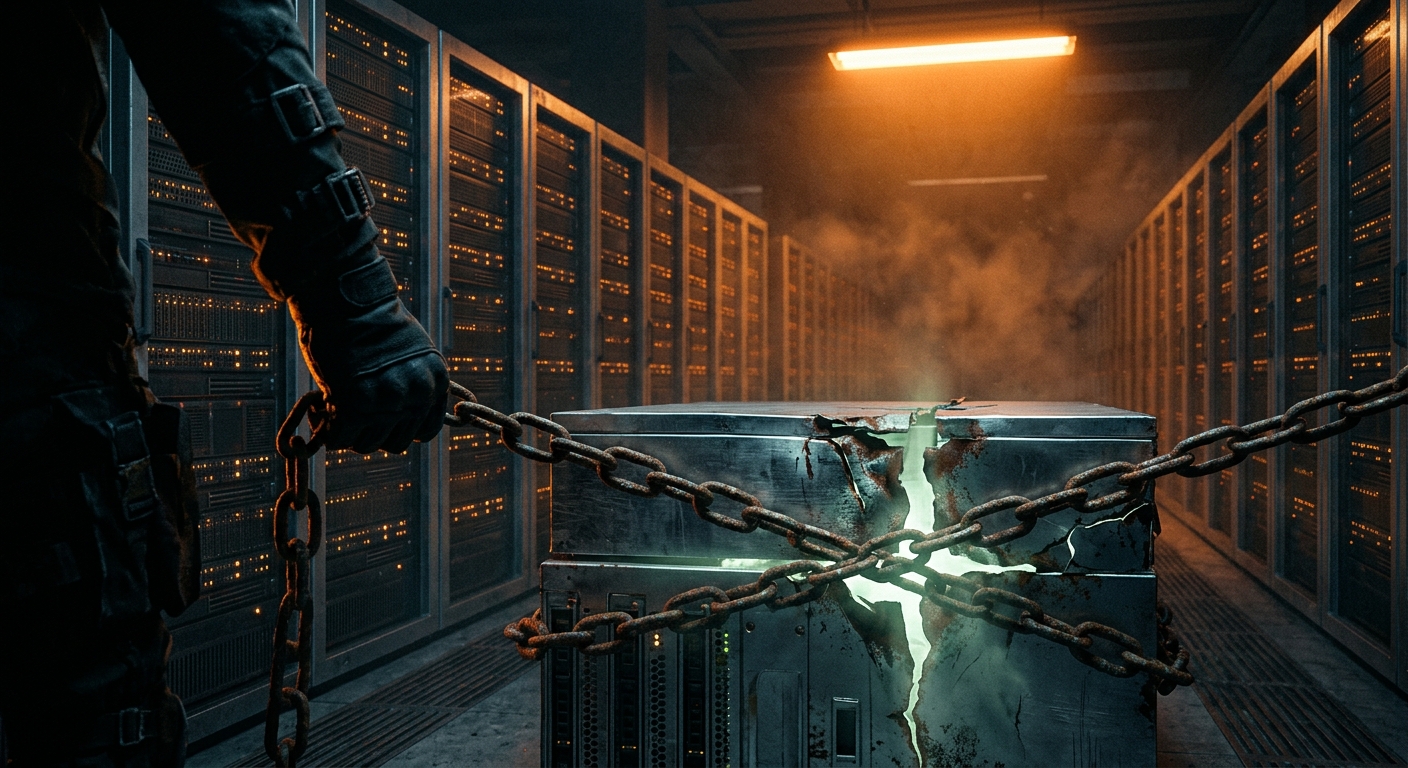
Introduction: With the increasing digitization of government services and the vast amount of sensitive data they handle, the government sector faces significant cybersecurity challenges. Cyberattacks targeting government entities pose risks to national security, citizen privacy, and critical infrastructure. This article provides an in-depth analysis of breaches in the government sector, their impact, and actionable strategies to enhance cybersecurity defenses.
I. Understanding Breaches in the Government Sector:
II. Key Threats and Attack Vectors:
III. Strengthening Government Cybersecurity Defenses:
IV. Collaboration and Information Sharing:
Conclusion: As cyber threats evolve, securing government systems and data becomes paramount to protect national security, citizen privacy, and critical infrastructure. By implementing robust cybersecurity measures, fostering a culture of security awareness, and promoting collaboration, the government sector can strengthen its defenses against breaches. Continuous monitoring, proactive risk management, and a swift and coordinated incident response are crucial in maintaining public trust and safeguarding sensitive information in today’s rapidly evolving threat landscape.
Disclaimer: This article provides general information and guidance about breaches in the government sector and strengthening cybersecurity. It is not legal or professional advice. Government entities should consult with cybersecurity professionals and adhere to specific regulatory requirements to ensure the protection of their systems, citizen data, and critical infrastructure.
5 notable government sector breaches
Office of Personnel Management (OPM) Breach (2014-2015):
U.S. National Archives and Records Administration (NARA) Breach (2011):
U.S. Office of Management and Budget (OMB) Breach (2013):
German Federal Foreign Office (FFO) Cyberattack (2018):
Australian Parliament House Cyberattack (2019):
Responses and actions taken to address these breaches varied depending on the incident and the respective government agencies involved. Common measures included incident response investigations, coordination with law enforcement agencies, implementation of enhanced security controls, and strengthening of network defenses. For the most up-to-date and detailed information on these incidents, it is advisable to consult reliable sources and official statements from the respective government agencies affected.