On November 8, 2025, analytics giant Mixpanel fell victim to a sophisticated SMS phishing attack that would ultimately expose customer data across hundreds of major organizations—from OpenAI and PornHub to SoundCloud and cryptocurrency platforms. The breach highlights critical vulnerabilities in the analytics industry, where third-party providers collect massive amounts of behavioral data about millions of users, creating high-value targets for sophisticated threat actors.
Executive Summary
What Happened: Mixpanel, a major web and mobile analytics provider with approximately 8,000 corporate customers, suffered a security breach on November 8, 2025, following a successful smishing (SMS phishing) campaign targeting its employees.
Who Was Affected: Confirmed victims include OpenAI (API users), CoinTracker, CoinLedger, SwissBorg, PornHub (Premium members), and SoundCloud (20% of users, approximately 28 million accounts). The full scope remains unclear, but with each customer potentially having millions of users, the total impact could affect hundreds of millions of people.
What Was Stolen: The type of exposed data varies by customer configuration but generally includes names, email addresses, location data, device information, behavioral analytics, and user activity patterns—precisely the kind of metadata that enables highly targeted phishing and social engineering attacks.
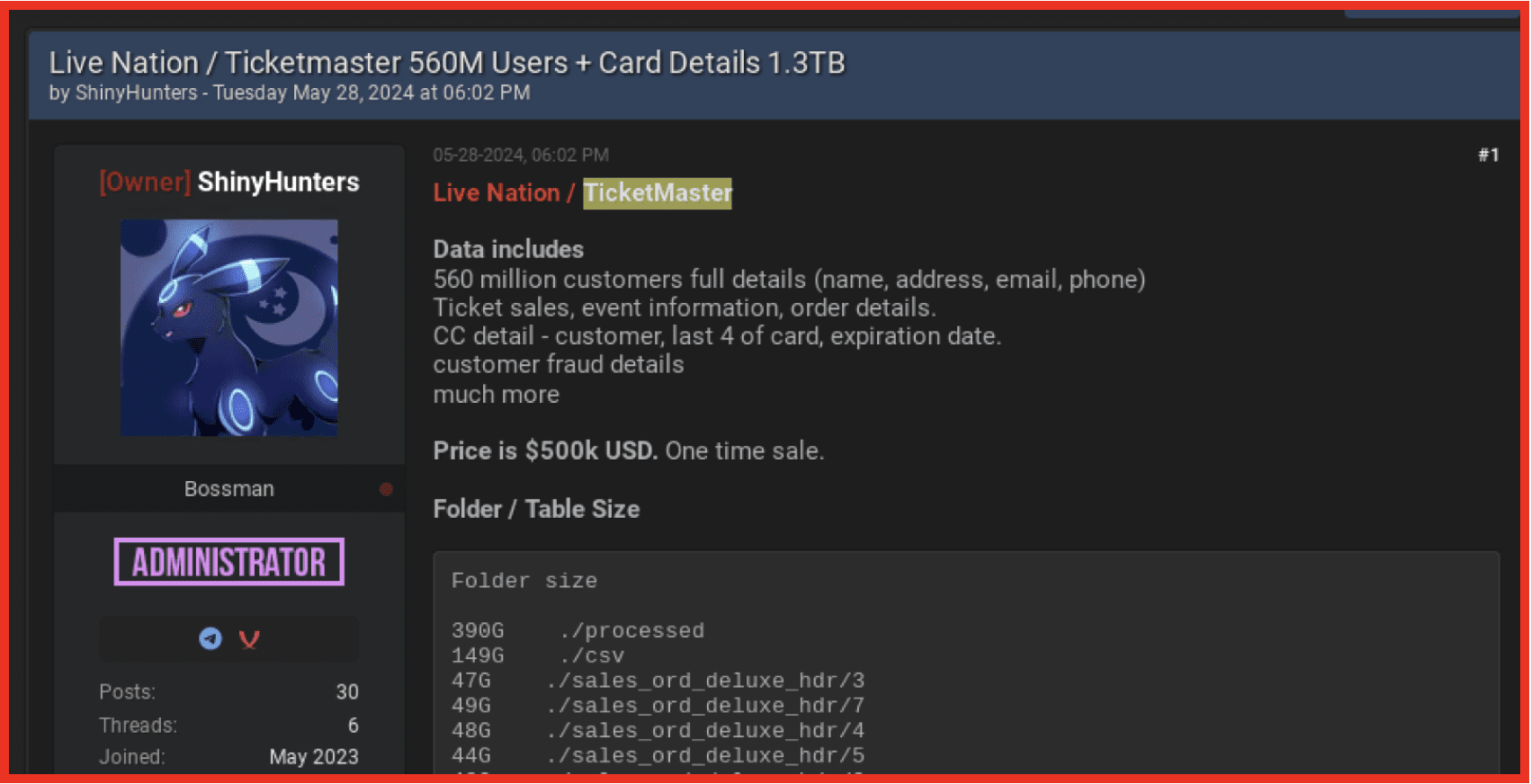
 Who’s Responsible: ShinyHunters, the notorious cybercrime group behind some of 2025’s most significant breaches, has claimed responsibility and is actively extorting affected customers.
Who’s Responsible: ShinyHunters, the notorious cybercrime group behind some of 2025’s most significant breaches, has claimed responsibility and is actively extorting affected customers.
Current Status: Mixpanel claims to have contained the breach, while ShinyHunters continues extortion campaigns. Several major customers including OpenAI have terminated their relationships with Mixpanel.
Understanding Mixpanel: The Analytics Giant You’ve Never Heard Of
Mixpanel is one of the largest web and mobile analytics companies operating behind the scenes of thousands of apps and websites you likely use every day. Founded in 2009 and serving approximately 8,000 corporate customers, Mixpanel provides event analytics that help companies understand how users interact with their products.
How Mixpanel Works
When you use an app or website that has integrated Mixpanel, a piece of tracking code embedded in the application monitors your every action:
- Every click, tap, and swipe you make
- Every page or screen you visit
- How long you spend on each section
- What features you use most frequently
- Your device information: screen size, operating system, browser version
- Your network details: whether you’re on WiFi or cellular, carrier name
- Your approximate location: derived from IP address
- Session duration and frequency: when and how often you use the app
This creates what security experts call a “digital shadow”—a detailed behavioral profile of how you interact with digital services. For legitimate businesses, this data helps improve user experience and product development. For attackers who steal it, this same data becomes ammunition for highly personalized attacks.
The Scale of Mixpanel’s Data Collection
With 8,000 corporate customers and each customer potentially serving millions of users, Mixpanel’s systems likely contain behavioral data on hundreds of millions to potentially billions of people worldwide. This concentration of sensitive information makes analytics providers like Mixpanel extraordinarily valuable targets for cybercriminals.
The Attack: November 8, 2025
Initial Compromise via Smishing
On November 8, 2025, threat actors launched a targeted SMS phishing (smishing) campaign against Mixpanel employees. Smishing attacks use deceptive text messages to trick recipients into revealing credentials or clicking malicious links.
Attack Methodology:
- Social Engineering: Attackers likely researched Mixpanel’s organizational structure to identify high-value employee targets
- Credential Harvesting: Deceptive SMS messages convinced employees to divulge authentication credentials
- MFA Bypass: The attackers successfully bypassed multi-factor authentication—though Mixpanel has not disclosed how this was accomplished
- Lateral Movement: Once inside, attackers pivoted through Mixpanel’s internal environment to access customer data repositories
Detection and Timeline
November 8, 2025: Mixpanel’s security operations center detected the smishing campaign and unauthorized access
November 9, 2025: Attackers exfiltrated datasets containing customer identifiable information and analytics data
November 21-25, 2025: Mixpanel began notifying affected customers about the breach (16-day delay from detection to customer notification for some victims)
November 27, 2025: Mixpanel publicly disclosed the incident in a bare-bones blog post just before the U.S. Thanksgiving holiday
December 2025: Major customers began publicly disclosing their involvement and ShinyHunters initiated extortion campaigns
Mixpanel’s Immediate Response
According to CEO Jen Taylor, Mixpanel took the following actions upon detecting the breach:
- Secured affected accounts immediately
- Revoked all active sessions and sign-ins
- Rotated compromised credentials
- Blocked threat actor IP addresses
- Reset passwords for all employees
- Implemented new security controls
- Engaged external cybersecurity partners for incident response
The Victims: A Growing List of Compromised Organizations
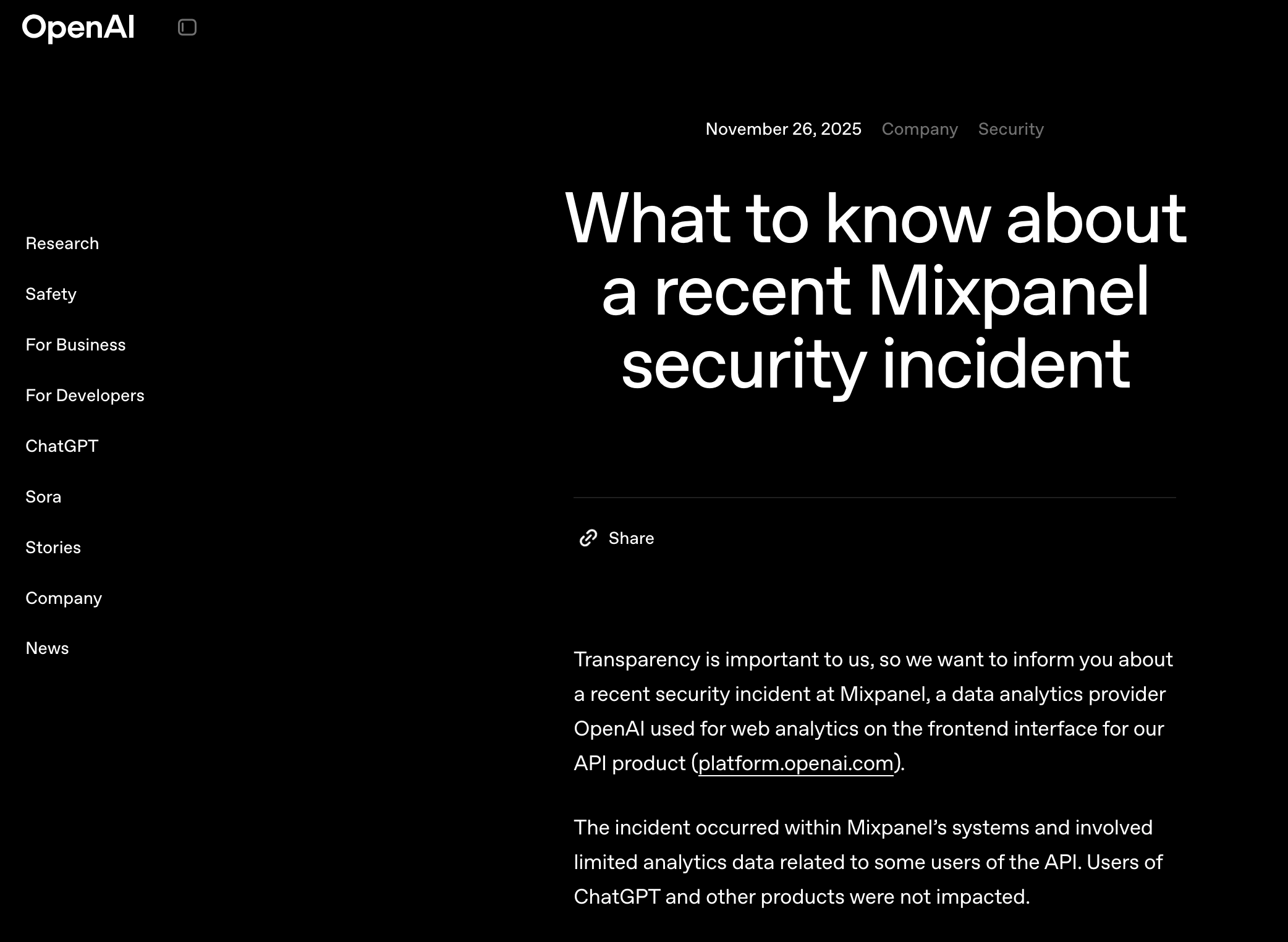
OpenAI: The First Major Disclosure
Disclosed: November 27, 2025
OpenAI became the first major customer to publicly acknowledge being affected by the Mixpanel breach. The AI company used Mixpanel to track user interactions on its API platform (platform.openai.com).
Exposed Data:
- Names provided on API accounts
- Email addresses associated with accounts
- Approximate location (city, state, country) based on IP addresses
- Operating system and browser information
- Referring websites
- Organization or User IDs associated with API accounts
The $7 Million Betrayal: Inside the xAI-OpenAI Trade Secret Theft CaseBreaking: Former xAI engineer accused of uploading entire codebase to personal systems before joining OpenAI in explosive trade secret lawsuit The artificial intelligence industry’s fierce talent wars have erupted into federal court, with Elon Musk’s xAI filing an explosive lawsuit against a former engineer accused of stealing the company’s most![]() Breached CompanyBreached Company
Breached CompanyBreached Company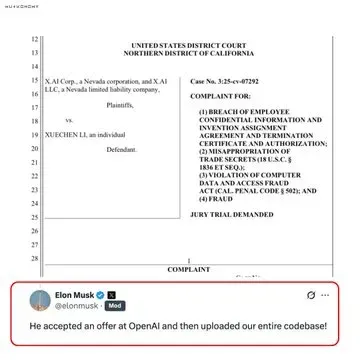 Impact: API users only—ChatGPT users were not affected. The exposed metadata could enable highly convincing phishing campaigns against developers and organizations using OpenAI’s API.
Impact: API users only—ChatGPT users were not affected. The exposed metadata could enable highly convincing phishing campaigns against developers and organizations using OpenAI’s API.
OpenAI’s Response:
- Immediately terminated use of Mixpanel across all production services
- Launched comprehensive security review of entire vendor ecosystem
- Elevated security requirements for all partners and vendors
- Directly notified all affected users and organizations
- Stressed that no API keys, passwords, chat content, or payment details were compromised
CoinTracker: Cryptocurrency Platform Exposure
Disclosed: November 27, 2025
CoinTracker, a cryptocurrency portfolio tracker and tax platform, confirmed exposure of customer data.
Exposed Data:
- Email addresses
- Location derived from IP addresses
- Device metadata
- Limited transaction count summaries
Significance: The targeting of cryptocurrency platforms suggests ShinyHunters may have been specifically seeking wallet associations and transaction patterns for potential follow-up attacks.
CoinLedger: Additional Crypto Platform Impact
Disclosed: December 2025
CoinLedger, another cryptocurrency tax and portfolio tracking service, also confirmed being affected.
Exposed Data:
- First and last names (if set in user profiles)
- Email addresses
- Transaction-related metadata
Risk: Users who provided names for tax reporting purposes face elevated phishing risks, as attackers can craft highly personalized messages.
SwissBorg: European Cryptocurrency Platform
Disclosed: December 2025
SwissBorg, a European cryptocurrency wealth management platform, was confirmed as an affected Mixpanel customer, though specific details about the exposed data remain limited.
PornHub: The Controversial Disclosure
Disclosed: December 13, 2025
Adult entertainment platform PornHub disclosed that “select Premium users” were affected by the Mixpanel breach, though the situation is complicated by conflicting claims about the data’s origin.
PornHub’s Claims:
- Data came from Mixpanel’s November 2025 breach
- Only affects users from before 2021, when PornHub stopped using Mixpanel
- All data is at least 4 years old
ShinyHunters’ Claims:
- 94GB of data containing 201,211,943 records
- Includes detailed viewing history, search queries, downloads
- Contains records as recent as 2023 (contradicting PornHub’s timeline)
- Currently extorting PornHub with threats to publish the data
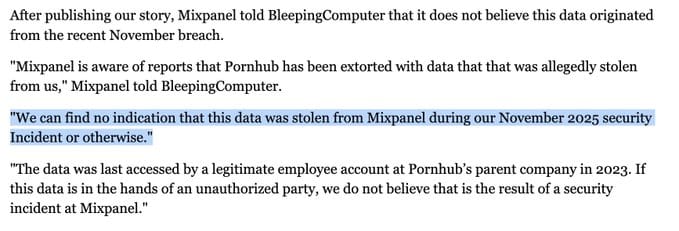
Mixpanel’s Rebuttal: In a statement to BleepingComputer, Mixpanel disputed that PornHub data came from the November breach:
“We can find no indication that this data was stolen from Mixpanel during our November 2025 security incident or otherwise. The data was last accessed by a legitimate employee account at Pornhub’s parent company in 2023. If this data is in the hands of an unauthorized party, we do not believe that is the result of a security incident at Mixpanel.” Exposed Data (according to samples reviewed by security researchers):
- Email addresses tied to Premium accounts
- Complete viewing history including video URLs and titles
- Search queries and keywords
- Download activity records
- Geographic location data
- Activity timestamps
- Activity types (watched, downloaded, viewed channel)
Significance: This represents one of the most sensitive data exposures of 2025, with severe implications for blackmail, extortion, and privacy violations. The dispute over the data’s origin suggests either a separate breach at PornHub’s parent company Aylo, or that multiple datasets from different time periods have been combined.
SoundCloud: Mass User Data Exposure
Disclosed: December 13, 2025
Music streaming platform SoundCloud confirmed a breach affecting approximately 20% of its user base—roughly 28 million accounts—following days of VPN connectivity issues reported by users.
Exposed Data:
- Email addresses
- Information already visible on public SoundCloud profiles
- No financial data or passwords compromised
Associated Attacks: Following the data breach, SoundCloud experienced:
- Multiple denial-of-service (DoS) attacks
- Two severe DoS incidents that temporarily took the website offline
- VPN access disruptions caused by security configuration changes
SoundCloud’s Response:
- Activated incident response protocols
- Engaged independent cybersecurity experts
- Enhanced monitoring and threat detection systems
- Reviewed and reinforced identity and access controls
- Implemented configuration changes (which inadvertently disrupted VPN access)
Attribution: Security sources confirmed to BleepingComputer that ShinyHunters is responsible for the SoundCloud breach and is now extorting the company.
Unknown Additional Victims
Given that Mixpanel has approximately 8,000 customers and CEO Jen Taylor stated only that “all impacted customers have been contacted directly,” the true scope of the breach remains unclear. Many affected organizations may not have publicly disclosed their involvement.
ShinyHunters: The Threat Actor Behind the Breach
ShinyHunters, tracked by Google Threat Intelligence as UNC6040, has claimed responsibility for the Mixpanel breach and is actively conducting extortion campaigns against affected customers. As detailed in our comprehensive analysis of ShinyHunters’ evolution, this group has transformed from Pokémon-inspired database thieves in 2020 into one of the most dangerous cybercrime operations of 2025.
2025: A Year of Unprecedented Success
The Mixpanel breach is just the latest in ShinyHunters’ remarkable 2025 campaign:
Salesforce Supply Chain Attacks:
- Salesloft Drift breach (August 2025): ~760 companies affected
- Gainsight breach (November 2025): 285+ Salesforce instances compromised
- Combined impact: Nearly 1,000 organizations
Other Major 2025 Breaches:
- Oracle E-Business Suite zero-day exploitation (CVE-2025-61884)
- Red Hat GitLab server: 28,000+ repositories stolen
- Discord third-party breach: User data exposed
- Multiple insurance companies including Allianz Life
- Major airlines including Qantas (5 million records)
Total 2025 Impact: ShinyHunters claims to have compromised approximately 1,500 organizations and stolen data affecting over 1 billion users. This includes the massive Google Salesforce breach affecting 2.5 billion Gmail users and dozens of other major organizations documented in our August 2025 unprecedented attack wave overview.
Extortion Tactics
ShinyHunters has begun sending extortion emails to Mixpanel customers that begin with “We are ShinyHunters” and threaten to publish stolen data unless ransom demands are paid in Bitcoin.
Extortion Strategy:
- Direct victim contact: Emails sent to compromised organizations
- Data sampling: Providing samples to prove legitimacy of stolen data
- Publication threats: Deadlines for payment before public release
- Media engagement: Confirming attacks to security researchers to increase pressure
The Scattered LAPSUS$ Hunters Collective
ShinyHunters operates as part of Scattered LAPSUS$ Hunters—a merger of three notorious cybercrime groups:
- ShinyHunters: Data theft and underground marketplace operations
- Scattered Spider: Social engineering and sophisticated targeting
- LAPSUS$: Destructive attacks and high-profile victims
This collective represents one of the most dangerous English-speaking cybercrime syndicates currently operating, with Microsoft describing them as “one of the most dangerous financially motivated threat groups.” Our investigation into the Crimson Collective alliance provides deeper insight into how these groups merged to create an unprecedented cybercrime supergroup.
The Data at Risk: Why Analytics Breaches Matter
The Power of Behavioral Metadata
While many people focus on “sensitive data” like passwords or payment information, the behavioral metadata collected by analytics platforms can be equally—or more—damaging in the hands of attackers.
What Attackers Can Do With Analytics Data:
1. Hyper-Targeted Phishing: With names, email addresses, location data, and usage patterns, attackers can craft extremely convincing phishing emails that reference:
- Specific products or services the victim actually uses
- Legitimate-looking account alerts based on real usage patterns
- Geographic details that add authenticity
- Device and browser information that mimics real system messages
2. Social Engineering: Behavioral data reveals:
- When users are most active (optimal timing for attacks)
- What features they use most (context for convincing requests)
- Company affiliations and organizational structures
- Technology stack and platform preferences
3. Account Takeover Preparation: Analytics data helps attackers:
- Identify high-value targets based on usage intensity
- Understand normal behavior patterns to avoid detection
- Build profiles for credential stuffing attacks
- Map relationships between users and organizations
4. Corporate Espionage: For business customers, leaked analytics reveal:
- Product development priorities and timelines
- User adoption rates and engagement metrics
- Feature usage that indicates business strategies
- Customer retention and churn patterns
The “Shadow Profile” Problem
Every time you interact with an app or website using Mixpanel (or similar analytics), you’re creating what privacy advocates call a “shadow profile”—a detailed record of your behavior that you never explicitly consented to and may not even know exists.
These profiles:
- Persist long after you stop using a service
- Can be cross-referenced with other data breaches
- May reveal sensitive information through behavioral patterns
- Create permanent attack surfaces even if you practice good security hygiene
Technical Analysis: How the Breach Unfolded
The Attack Chain
Phase 1: Initial Access (November 8)
- Smishing campaign targets Mixpanel employees
- Social engineering convinces victims to provide credentials
- MFA bypass achieved (method undisclosed by Mixpanel)
Phase 2: Reconnaissance
- Attackers explore Mixpanel’s internal environment
- Identify customer data repositories
- Map analytics data storage systems
- Locate high-value targets (cryptocurrency platforms, adult content, major tech companies)
Phase 3: Exfiltration (November 9)
- Systematic extraction of customer datasets
- Data exported through legitimate Mixpanel interfaces designed for customer data access
- Multiple export methods likely used: UI exports, API calls, data pipeline exports
Phase 4: Post-Exploitation
- 16-day period before some customers were notified
- Data analysis and victim prioritization by ShinyHunters
- Extortion campaign planning
- Public disclosure timing (before Thanksgiving holiday weekend)
Security Failures
1. Employee Credential Compromise: Despite being a technology company handling sensitive customer data, Mixpanel employees fell victim to a smishing campaign—suggesting insufficient security awareness training or ineffective anti-phishing controls.
2. MFA Bypass: The attackers successfully bypassed multi-factor authentication. Mixpanel has not disclosed whether this was due to:
- MFA fatigue attacks (bombarding users with authentication prompts)
- Session hijacking
- Compromise of MFA recovery mechanisms
- Inadequate MFA implementation (SMS-based rather than hardware tokens)
3. Delayed Detection: While Mixpanel detected the attack on November 8, exfiltration occurred on November 9, and some customers weren’t notified until November 25—a 16-day gap that gave attackers significant time to analyze stolen data and plan extortion campaigns.
4. Data Access Controls: The attackers were able to export large datasets containing customer information, suggesting:
- Overly permissive internal access controls
- Insufficient monitoring of bulk data exports
- Lack of data loss prevention systems
- Inadequate segmentation between customer datasets
Transparency Controversy: Mixpanel’s Inadequate Disclosure
The Thanksgiving Holiday Announcement
Mixpanel’s November 27 disclosure—released just before the U.S. Thanksgiving holiday weekend—drew sharp criticism from the security community for its timing and lack of detail.
Problems With the Initial Disclosure:
1. Minimal Information: CEO Jen Taylor’s initial blog post was remarkably sparse, stating only that:
- A security incident was detected on November 8
- “Some customers” were affected (no number provided)
- The company had taken actions to “eradicate unauthorized access”
- Affected customers were being contacted directly
2. Critical Omissions: The initial disclosure failed to mention:
- That customer data had actually been stolen (not just accessed)
- What types of data were compromised
- How many customers were affected
- How the breach occurred
- Whether there was ongoing risk to customers
3. Holiday Timing: Releasing the disclosure before a major U.S. holiday ensured minimal media coverage and gave affected customers less time to respond before taking holiday time off.
4. Lack of Transparency: Mixpanel CEO Jen Taylor did not respond to multiple media inquiries from TechCrunch and other outlets seeking clarification about:
- Communication from the attackers
- Ransom demands
- Whether employee accounts had MFA protection
- The full scope of affected customers
- Timeline details
Industry Criticism
Security experts described Mixpanel’s handling of the disclosure as potentially “setting a new standard for how not to announce a data breach.”
Key Concerns:
- Failure to explicitly state that data was exfiltrated, not just accessed
- Lack of guidance for affected users on protective measures
- No clear timeline of events
- Minimal technical details about the attack vector
- Apparent attempt to minimize the incident’s severity
Contrast With Customer Disclosures: It was only through OpenAI’s more detailed disclosure two days later that the public learned customer data had actually been stolen from Mixpanel’s systems. This forced subsequent customers to be more transparent than Mixpanel itself had been.
The Attribution Dispute: Where Did the PornHub Data Come From?
One of the most intriguing aspects of this breach is the conflicting claims about the PornHub dataset’s origin.
Three Competing Narratives
PornHub’s Position:
- Data came from Mixpanel’s November 2025 breach
- All exposed data is from 2021 or earlier
- PornHub stopped using Mixpanel in 2021
ShinyHunters’ Claims:
- Data was stolen in the Mixpanel breach
- Dataset includes records as recent as 2023
- Contains 201 million+ records of detailed user activity
Mixpanel’s Rebuttal:
- Data was NOT stolen in the November breach
- Last access was by a “legitimate employee account at Pornhub’s parent company in 2023”
- Not the result of any Mixpanel security incident
Possible Scenarios
Scenario 1: Multiple Breaches The PornHub data could have originated from a separate breach of Aylo (PornHub’s parent company) systems in 2023, not from Mixpanel at all. ShinyHunters may be conflating or bundling datasets from different breaches.
Scenario 2: Compromised Employee Credentials Mixpanel’s claim that data was “accessed by a legitimate employee account” suggests Aylo employee credentials may have been compromised, either:
- In the 2023 timeframe (credentials held for 2 years before exploitation)
- Through a separate phishing campaign targeting Aylo employees
- Via credential reuse from other breaches
Scenario 3: Historical Data Retention Even though PornHub stopped actively using Mixpanel in 2021, Mixpanel may have retained historical analytics data. The 2023 access by an Aylo employee could have been legitimate, but the data repository was then targeted in the November 2025 breach.
Scenario 4: Mixpanel’s November Breach + Historical Access Both could be true: ShinyHunters gained access to Mixpanel systems in November 2025 and discovered historical data that had been accessed by Aylo employees in 2023 but never deleted.
Implications
Regardless of the true origin, this dispute highlights:
- Data retention problems: Analytics providers keeping customer data years after relationships end
- Access control failures: Questions about who had legitimate access to old data repositories
- Attribution complexity: Difficulty determining breach sources in multi-layered technology stacks
- Vendor accountability: Unclear who bears responsibility when data persists after contracts end
Lessons for Organizations: The Third-Party Risk Crisis
The Mixpanel breach exemplifies a critical challenge facing modern organizations: third-party vendor risk has become one of the most significant attack vectors in cybersecurity.
The Analytics Provider Risk
Why Analytics Companies Are High-Value Targets:
1. Data Concentration: A single analytics provider breach can expose data from thousands of companies and potentially billions of users—creating economies of scale for attackers.
2. Behavioral Intelligence: Unlike payment processors or authentication providers that handle narrow data types, analytics platforms collect rich behavioral data that’s valuable for multiple attack types.
3. Integration Depth: Analytics code runs on millions of websites and apps, often with extensive access to user activity, creating broad attack surfaces.
4. Historical Data Retention: Many analytics providers retain years of historical data, creating ongoing liability long after business relationships end.
5. Regulatory Gaps: Analytics providers face less regulatory scrutiny than financial institutions or healthcare companies, despite handling similarly sensitive data.
Key Vulnerabilities Exposed
1. The “Trust Tax”: Organizations implicitly trust third-party vendors with access to customer data, often without conducting rigorous ongoing security assessments.
2. Visibility Gaps: Most companies don’t know:
- Exactly what data their analytics providers collect
- How long that data is retained
- Who has access to it within the vendor’s organization
- What security controls protect it
3. Vendor Security Assumptions: Organizations assume major vendors have enterprise-grade security, but the Mixpanel breach demonstrates that even established providers can fall victim to relatively simple attacks like smishing.
4. Incident Response Dependencies: When vendors are breached, customers depend entirely on the vendor’s transparency and timeliness in disclosure—as evidenced by Mixpanel’s 16-day delay in notifying some customers.
5. Historical Data Liability: The PornHub situation demonstrates that organizations face ongoing risk from data held by former vendors, potentially years after contracts end.
Recommendations for Organizations
Immediate Actions
1. Audit Analytics Integrations:
- Identify all analytics and tracking services embedded in your applications
- Review what data each service collects
- Verify business justification for each integration
- Assess whether the risk/benefit ratio still makes sense
2. Review Vendor Contracts:
- Verify data retention policies and deletion timelines
- Confirm contractual obligations for breach notification
- Establish maximum data retention periods
- Include specific security requirements in contracts
3. Implement Data Minimization:
- Configure analytics platforms to collect only essential data
- Exclude PII where possible
- Use anonymization and pseudonymization techniques
- Disable features that collect unnecessary device or location data
4. Monitor for Compromise: If you use Mixpanel or similar platforms:
- Review logs for unusual export activity
- Watch for phishing campaigns targeting your users
- Monitor dark web and breach forums for your data
- Consider email domain monitoring services
5. Prepare User Communications:
- Draft template breach notifications
- Establish communication protocols
- Prepare FAQs for customer questions
- Have PR and legal teams ready to respond
Long-Term Strategy
1. Zero Trust for Vendors:
- Never assume third-party security is adequate
- Conduct regular security assessments of critical vendors
- Require SOC 2 Type II reports as a minimum
- Perform your own penetration testing where contracts allow
2. Vendor Security Requirements:
- Mandate MFA using hardware tokens or authenticator apps (not SMS)
- Require security awareness training for vendor employees
- Establish incident response SLAs in contracts
- Include security breach insurance requirements
3. Data Governance:
- Implement data classification systems
- Map data flows through your vendor ecosystem
- Establish clear data ownership and deletion policies
- Regularly audit third-party data holdings
4. Alternative Approaches:
- Consider self-hosted analytics solutions (e.g., Matomo, Plausible)
- Evaluate privacy-focused alternatives that collect less data
- Build in-house analytics capabilities for sensitive applications
- Use multiple smaller vendors instead of concentrating risk
5. Incident Response Planning:
- Include vendor breaches in IR playbooks
- Establish procedures for evaluating vendor incidents
- Prepare communication plans for various breach scenarios
- Conduct tabletop exercises that include third-party compromises
Recommendations for Users
If You Use Affected Services
1. Verify Your Impact:
- Check whether your accounts with OpenAI, CoinTracker, SoundCloud, or other services were affected
- Look for official breach notifications from the companies
- Don’t trust unsolicited emails claiming to be breach notifications
2. Immediate Security Actions:
- Enable multi-factor authentication on all affected accounts
- Use authenticator apps or hardware tokens, not SMS
- Change passwords if you’ve reused them across services
- Review account activity for unauthorized access
3. Monitor for Attacks:
- Watch for phishing emails that reference your account details
- Be suspicious of messages that create urgency
- Verify sender addresses carefully (attackers will spoof official emails)
- Never click links in unexpected security-related emails
4. Financial Monitoring:
- For cryptocurrency platform users: Monitor wallets for unusual activity
- Check credit reports for signs of identity theft
- Consider fraud alerts or credit freezes if concerned
- Watch for tax-related identity theft
5. Long-Term Vigilance:
- This data can be used in attacks months or years from now
- Maintain heightened awareness for social engineering attempts
- Regularly search for your email on breach notification sites (haveibeenpwned.com)
- Consider using unique email addresses for different services
General Privacy Practices
1. Minimize Data Sharing:
- Provide minimal information when signing up for services
- Use privacy-focused email aliases (e.g., Apple Hide My Email, SimpleLogin)
- Avoid connecting social media accounts unless necessary
- Review and revoke unnecessary app permissions
2. Use Privacy Tools:
- Browser extensions that block trackers (uBlock Origin, Privacy Badger)
- VPN services for additional privacy (though note SoundCloud’s VPN issues)
- Privacy-focused browsers (Firefox, Brave)
- Regular clearing of cookies and browsing data
3. Understand What’s Collected:
- Review privacy policies of services you use
- Understand that “free” services monetize your data
- Consider paid alternatives that don’t rely on data collection
- Use services’ data export features to see what they’ve collected
The Broader Implications: Analytics Industry Under Scrutiny
The Mixpanel breach represents more than just another data breach—it highlights fundamental questions about the analytics industry’s business model and privacy practices.
The Surveillance Economy
Analytics companies like Mixpanel are part of a vast surveillance economy that:
- Collects billions of data points about human behavior
- Operates largely invisibly to end users
- Monetizes detailed behavioral profiles
- Creates massive honeypots of sensitive data
- Faces minimal regulatory oversight compared to impact
Regulatory Pressure Building
Current Regulatory Landscape:
- GDPR in Europe requires disclosure of third-party data sharing
- CCPA in California gives users some data deletion rights
- Most jurisdictions lack specific analytics provider regulations
Expected Future Developments:
- Increased scrutiny of behavioral tracking technologies
- Potential mandatory disclosure requirements for embedded trackers
- Enhanced breach notification requirements
- Stricter data retention limits
- Potential liability for poor vendor security
Industry Changes Needed
1. Transparency:
- Clear disclosure of what data is collected and how it’s used
- Visibility into data retention policies
- Regular audits and public security reports
2. Data Minimization:
- Collection limited to what’s actually necessary for stated purposes
- Aggressive deletion of historical data
- Anonymization by default
3. Security Standards:
- Industry-wide minimum security requirements
- Regular third-party security audits
- Incident response preparedness
- Employee security training standards
4. User Control:
- Easy opt-out mechanisms
- Data export and deletion capabilities
- Granular control over what data is collected
OpenAI’s Response: A Case Study in Vendor Management
OpenAI’s handling of the Mixpanel breach provides a model for how organizations should respond to third-party vendor compromises.
Immediate Actions Taken
1. Vendor Termination: OpenAI immediately and completely terminated its use of Mixpanel across all production services—a decisive action that many organizations hesitate to take due to operational dependencies.
2. Comprehensive Security Review: Launched an expanded security review of the entire vendor ecosystem, not just analytics providers, recognizing that similar vulnerabilities could exist elsewhere.
3. Elevated Requirements: Implemented new, higher security requirements for all partners and vendors, effectively raising the bar across their supply chain.
4. Transparent Communication: Published a detailed public advisory explaining:
- Exactly what data was exposed
- What was NOT affected (API keys, passwords, chat content)
- Steps users should take
- OpenAI’s remediation actions
Why This Matters
OpenAI’s response demonstrates that:
- Vendor relationships aren’t sacred: When security fails, termination must be on the table
- Transparency builds trust: Detailed disclosure, even when embarrassing, maintains customer confidence
- Systemic fixes are essential: One vendor breach should trigger ecosystem-wide review
- Speed matters: Quick decisive action limits exposure and demonstrates commitment to security
The ShinyHunters Factor: Why Attribution Matters
Knowing that ShinyHunters is behind the Mixpanel breach provides important context for understanding the threat landscape.
ShinyHunters’ Track Record
Sophistication Level: High
- Successfully compromised some of 2025’s most secure organizations
- Demonstrates advanced social engineering capabilities
- Operates sophisticated extortion campaigns
- Maintains operational security despite law enforcement pressure
Motivation: Financial
- Primarily seeks to monetize stolen data through extortion
- Occasionally sells data on underground marketplaces
- Not state-sponsored or ideologically motivated
Tactics Evolution:
- Early days: Opportunistic breaches, database theft
- Current: Sophisticated supply chain attacks targeting SaaS platforms
- Future: Development of ShinySpid3r ransomware-as-a-service
Implications for Victims
1. Professional Extortion: ShinyHunters will likely conduct persistent, professional extortion campaigns with:
- Real deadlines for payment
- Proof-of-concept data releases
- Media engagement to increase pressure
- Potential data sale if extortion fails
2. Data Will Be Weaponized: Whether or not victims pay:
- Data will be used for future attacks
- Behavioral profiles will enhance social engineering
- Information may be combined with other breach data
- Secondary attacks against end users are likely
3. Long-Term Threat: ShinyHunters has demonstrated:
- Ability to hold compromised credentials for years
- Patience in planning attacks
- Resilience despite law enforcement actions
- Expanding capabilities (moving into ransomware)
What Comes Next: The Aftermath of Mixpanel
For Mixpanel
Immediate Challenges:
- Rebuilding customer trust after inadequate initial disclosure
- Potential loss of major customers beyond OpenAI
- Regulatory investigations likely in multiple jurisdictions
- Possible civil litigation from affected customers and users
- Need to invest heavily in security improvements
Long-Term Questions:
- Can Mixpanel recover its reputation in the security-conscious enterprise market?
- Will the company face significant customer churn?
- What regulatory penalties might be imposed?
- How will this affect the company’s valuation and future funding?
For the Industry
Analytics Provider Impact:
- Increased scrutiny of security practices across the sector
- Potential mass migration to privacy-focused alternatives
- Customer demands for enhanced security controls
- Higher insurance costs and security investment requirements
Broader Third-Party Risk:
- Organizations reassessing entire vendor ecosystems
- Increased due diligence requirements
- More aggressive vendor security audit programs
- Contractual changes to enhance breach notification and liability
For Users
Ongoing Risks:
- Stolen data remains usable for years
- Elevated phishing and social engineering threats
- Potential for identity theft and account takeover
- Secondary attacks leveraging behavioral profiles
Protective Actions:
- Maintain heightened security awareness
- Continue monitoring for breach notifications
- Implement strong authentication everywhere
- Consider privacy-focused alternatives when possible
Conclusion: The Third-Party Risk Reckoning
The Mixpanel breach of November 2025 serves as a stark reminder that in our interconnected digital ecosystem, security is only as strong as the weakest link in the vendor chain. When a single analytics provider serving 8,000 customers falls victim to a smishing attack, the reverberations can affect hundreds of millions of users worldwide.
Key Takeaways:
1. Analytics Providers Are Critical Infrastructure These companies collect vast amounts of behavioral data on billions of people, making them high-value targets. They deserve the same security scrutiny as financial institutions and healthcare providers.
2. Third-Party Risk Is First-Party Risk Organizations cannot outsource security. When vendors are breached, the customer organization bears the reputational and legal consequences, even if they did nothing wrong.
3. Transparency Matters Mixpanel’s inadequate initial disclosure undermined trust and set a poor example for the industry. OpenAI’s detailed response demonstrated the right approach.
4. Historical Data Is a Liability The PornHub controversy highlights that data retained years after relationships end creates ongoing risk. Aggressive data deletion policies aren’t just good privacy practice—they’re security necessities.
5. The Surveillance Economy Has Consequences The business model of collecting detailed behavioral data on millions of people creates massive honeypots that attract sophisticated attackers. This incident should prompt industry-wide reconsideration of data collection practices.
6. ShinyHunters Isn’t Going Away Despite law enforcement pressure, this group continues to successfully breach major organizations. Their evolution toward ransomware suggests escalating threats ahead.
7. Users Need Better Protection The current system places all risk on individuals who have no control over which analytics providers are embedded in the services they use. Regulatory intervention may be necessary to rebalance this equation.
As ShinyHunters continues its extortion campaigns and more affected organizations come forward, the full scope of the Mixpanel breach will become clearer. What’s already evident is that this incident represents a inflection point for the analytics industry—one that demands fundamental changes in how behavioral data is collected, protected, and retained.
The question now is whether the industry will embrace meaningful reform, or whether it will take additional breaches and regulatory intervention to force change. For the hundreds of millions of users whose behavioral data remains in circulation, the answer to that question matters greatly.
Status as of December 17, 2025:
- Extortion campaigns ongoing
- Full victim list still undisclosed
- Regulatory investigations likely pending
- OpenAI and potentially other major customers have terminated Mixpanel contracts
- ShinyHunters continues to threaten additional data releases
This article will be updated as new information emerges about affected organizations and the ongoing extortion campaigns.
References:
- Mixpanel CEO Jen Taylor blog post (November 27, 2025)
- OpenAI security advisory (November 27, 2025)
- BleepingComputer reporting on ShinyHunters extortion
- TechCrunch analysis of breach disclosure failures
- Multiple customer breach notifications (CoinTracker, SoundCloud, PornHub)