A comprehensive analysis of the ransomware-as-a-service operation that has compromised over 400 organizations worldwide through sophisticated SharePoint exploitation
Executive Summary
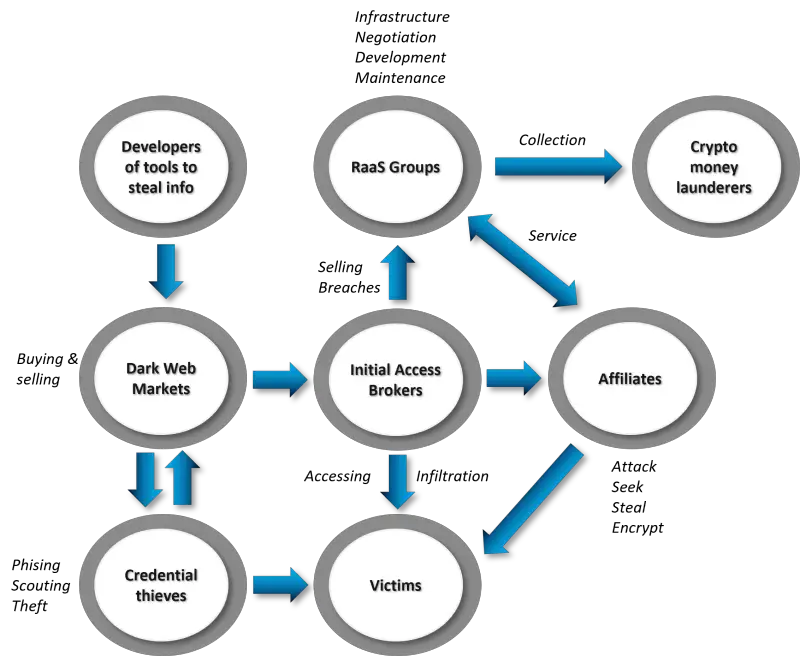
The emergence of Warlock ransomware in mid-2025 has fundamentally reshaped the global cybersecurity landscape, representing a new paradigm in the sophistication and scale of ransomware operations. Operating as a ransomware-as-a-service (RaaS) platform since June 2025, Warlock has rapidly evolved from a flashy cybercrime forum advertisement to one of the most closely watched ransomware threats of 2025, compromising over 400 SharePoint servers across 148 organizations within weeks of its first wave of attacks.
What sets Warlock apart from conventional ransomware operations is its unprecedented combination of zero-day exploitation capabilities, strategic targeting of critical infrastructure, and innovative data monetization strategies. The group has successfully breached major telecommunications providers including Colt Technology Services and French telecom giant Orange, auctioning stolen datasets for hundreds of thousands of dollars rather than employing traditional leak-and-pressure tactics.
Most concerning is Warlock’s attribution to Storm-2603, a China-based threat actor that blurs the lines between state-sponsored espionage and financially motivated cybercrime, raising critical questions about the evolving nature of nation-state cyber operations in the ransomware era.
The Birth of a Digital Predator: Warlock’s Rapid Ascension
Timeline of Terror
Warlock made its public debut on the Russian-language RAMP forum in early June 2025, advertising itself to potential affiliates with the tagline: “If you want a Lamborghini, please contact me.” This brazen marketing approach immediately distinguished the group from more traditional ransomware operations, signaling an aggressive growth strategy designed to attract high-caliber cybercriminals.
June 2025: Within just a few days after this flashy entrance, the group had already claimed at least 16 successful attacks, roughly half targeting government agencies in countries such as Portugal, Croatia, and Turkey.
July 2025: The timeline of activity shows rapid escalation: from forum promotion in early June, to deployment of ToolShell exploits in mid-July, to wide scale targeting by late July.
August 2025: The breach at Colt Technology Services, serving clients in over 30 countries, began on August 12 and was publicly disclosed two days later. On its leak site and underground forums, Warlock advertised more than 1 million exfiltrated documents for auction at $200,000, ending August 27.
A New Breed of Ransomware Economics
No ransom payment structures or affiliate revenue shares have been confirmed, but broader industry data suggests government-related ransomware incidents in 2025 carried an average demand of $2.4 million. However, Warlock’s innovation lies not just in ransom demands but in their data monetization strategy.
Rather than following the conventional ransomware playbook of leaking data samples to pressure victims, Warlock departed from standard ransomware tactics by refusing to leak data samples to pressure Colt. Instead, the group privately auctioned the entire dataset, a novel strategy intended to maximize profits and minimize public exposure.
This approach represents a fundamental shift in ransomware economics, treating stolen data as commodified assets to be sold to the highest bidder rather than mere leverage against the original victim.
The ToolShell Weapon: Deconstructing the Technical Arsenal
The Zero-Day Exploit Chain
The technical foundation of Warlock’s success lies in the “ToolShell” vulnerabilities (CVE-2025-49704, CVE-2025-49706, CVE-2025-53770, CVE-2025-53771). These vulnerabilities enable attackers to achieve full remote code execution (RCE) without requiring any credentials.
The exploit chain operates through a sophisticated two-stage attack:
Stage 1 - Authentication Bypass (CVE-2025-53771): The attacker sends a POST request to /_layouts/15/ToolPane.aspx?DisplayMode=Edit using a crafted Referer header (/_layouts/SignOut.aspx) to bypass authentication.
Stage 2 - Remote Code Execution (CVE-2025-53770): With that access, the attacker submits a malicious body to the same endpoint. SharePoint deserializes untrusted data and runs the embedded code, which plants a quiet ASPX web shell.
The Vulnerability Timeline: A Race Against Time
The rapid weaponization of these vulnerabilities demonstrates the evolving sophistication of threat actors:
- May 2025: At Pwn2Own Berlin, security researchers from Viettel Cyber Security demonstrated a chained exploit targeting on-premises SharePoint. This exploit combined CVE-2025-49704 (unsafe deserialization) and CVE-2025-49706 (path traversal/spoofing) to achieve unauthenticated remote code execution (RCE). The exploit chain was dubbed ToolShell.
- July 9, 2025: Microsoft issued fixes for CVE-2025-49704 and CVE-2025-49706. These were believed to fully address the ToolShell chain.
- July 18, 2025: Eye Security identified active exploitation of SharePoint servers in the wild using 0-day bypasses for the original ToolShell vulnerabilities.
- July 20, 2025: Microsoft acknowledged the attacks and issued an official advisory, assigning CVE-2025-53770 (new unsafe deserialization RCE) and CVE-2025-53771 (server spoofing vulnerability) to the bypass variants.
This timeline reveals how modern cyber threats are two-sided, combining an initial breach vector with a mechanism for long-term persistence, and demonstrates that threat actors are not merely discovering vulnerabilities, but also systematically reverse-engineering patches to weaponize bypasses.
Storm-2603: The Shadow Behind the Storm
Attribution and Geopolitical Implications
Warlock activity has been tied to the China-based actor tracked as Storm-2603, which has deployed the ransomware in at least 11 confirmed incidents since mid-July 2025. This attribution carries profound implications for understanding the evolving nature of state-sponsored cyber operations.
The group that Microsoft tracks as Storm-2603 is assessed with moderate confidence to be a China-based threat actor. Microsoft has not identified links between Storm-2603 and other known Chinese threat actors. However, Microsoft has observed two named Chinese nation-state actors, Linen Typhoon and Violet Typhoon, exploiting vulnerabilities targeting internet-facing SharePoint servers. In addition, we have observed another China-based threat actor, tracked as Storm-2603, exploiting these vulnerabilities.
The Hybrid Threat Model
What makes Storm-2603 particularly concerning is its apparent hybrid nature, operating at the intersection of state-sponsored capabilities and criminal motivations. This raises the possibility that Chinese nation-state actors may be purchasing access to ransomware tools or services from cybercriminal marketplaces, using them for both sanctioned operations and unsanctioned personal profit.
“We tend to assess it is a financially motivated actor, but with this, we can’t also exclude the option that this is a dual motivation actor, both espionage and financially motivated,” Sergey Shykevich, Threat Intelligence Group Manager at Check Point, told The Hacker News.
Technical Capabilities and Infrastructure
Storm-2603’s tactics, techniques, and procedures (TTPs), along with a technical breakdown of the ak47c2, a custom malware framework used in their attacks and their different ransomware payloads. The group demonstrates sophisticated capabilities including:
- DNS-controlled backdoor deployment
- BYOVD techniques to disable endpoint defenses and DLL hijacking to deploy multiple ransomware families
- The use of open-source tools such as PsExec and masscan
- A custom tool that leverages the BYOVD (Bring Your Own Vulnerable Driver) technique to tamper with endpoint protections
High-Profile Victims: Critical Infrastructure Under Siege
Colt Technology Services: A Global Network Compromised
On August 21, 2025, Colt Technology Services, a UK-based telecommunications and network services provider, disclosed that they had experienced a cyber incident involving unauthorized access to internal systems. The company confirmed that “some data has been taken,” following an earlier report of operational disruptions on August 12.
The impact was severe: The attack reportedly disrupted customer-facing services, including portals, voice APIs, and monitoring systems. According to BleepingComputer, Warlock claimed to have exfiltrated over one million documents containing financial records, network architecture details, and Colt’s customer data.
The British telecommunications and network services provider previously disclosed it suffered an attack on August 12, but this is the first time they confirmed data had been stolen. “A criminal group has accessed certain files from our systems that may contain information related to our customers and posted the document titles on the dark web,” reads an updated security incident advisory on Colt’s site.
Orange SA: French Telecom Giant Breached
Orange, France’s largest telecom operator, also confirmed a ransomware breach, with 4GB of sensitive business data published on the dark web by mid-August. The breach, which Orange disclosed and reported to national authorities at the end of July, targeted the company’s internal systems with ransomware associated with a gang calling itself Warlock.
The Broader Victim Landscape
According to Ransomware.live data, Warlock has primarily targeted technology companies (12 victims), telecommunications (3), financial services (2), and manufacturing (2). Geographically, the United States has been the most targeted (10 victims), followed by Japan (4), the United Kingdom (3), India (2), and France (2).
According to data supplied through the open source RansomLook.io information service, which is currently tracking 475 ransomware gangs across hundreds of dark web forums, markets and other channels, Warlock has claimed a total of 22 new victims since since 16 August, according to the data.
Technical Attack Methodology: Dissecting the Kill Chain
Initial Access and Persistence
Once inside, attackers deploy the spinstall0.aspx web shell, along with variants such as spinstall1.aspx and spinstall2.aspx. This shell is hosted within the w3wp.exe process and is used to extract ASP.NET MachineKey material, maintain access, and stage the ransomware payload.
What makes CVE-2025-53770 uniquely threatening is its methodology – the exploit chain, labeled “ToolShell.” ToolShell is engineered to play the long-game: attackers are not only gaining temporary access, but also taking the server’s cryptographic machine keys, specifically the ValidationKey and DecryptionKey. Possessing these keys allows threat actors to independently forge authentication tokens and __VIEWSTATE payloads, granting them persistent access that can survive standard mitigation strategies such as a server reboot or removing web shells.
Credential Harvesting and Lateral Movement
The threat actor performs credential access using Mimikatz, specifically targeting the Local Security Authority Subsystem Service (LSASS) memory to extract plaintext credentials. The actor moves laterally using PsExec and the Impacket toolkit, executing commands using Windows Management Instrumentation (WMI).
Once in a network, the attackers first establish higher privileges by creating a new Group Policy Object (GPO) within the domain. The attacker activates the built-in “guest” account on a Windows machine and modifies its password, enabling it to be used for access.
Data Exfiltration and Ransomware Deployment
Storm-2603 is then observed modifying Group Policy Objects (GPO) to distribute Warlock ransomware in compromised environments.
Warlock ransomware deployment is enabled by copying the ransomware binary into public folders on multiple endpoints via the Ingress transfer tool. The ransomware then encrypts files, before placing a ransom note titled “How to decrypt my data.txt” within affected directories.
The data exfiltration process is conducted using RClone, a legitimate open-source file synchronization tool. In one case observed by Trend Micro, the file was disguised as TrendSecurity.exe and placed in an inconspicuous directory to evade detection.
The LockBit Connection: Evolutionary Ransomware Development
Technical Lineage
The researchers observed that Warlock appears to be a customized derivative of the leaked LockBit 3.0 builder. This connection reveals important insights about ransomware evolution in 2025.
In mid-2025, threat actor Storm-2603 deployed both LockBit Black and Warlock in the same attack chains against SharePoint environments, using DLL sideloading via legitimate utilities like 7Zip. This suggests Warlock was constructed using the same builder framework that was made public in 2022, highlighting how a single leak enabled the proliferation of LockBit-based variants beyond the original.
Operational Connections
When the ransomware gang launched in March 2025, they used LockBit ransomware notes in their attacks, customized to include a Tox ID for ransom negotiations. In June, the ransomware gang branded itself as the “Warlock Group,” with customized ransom notes and dark web negotiation and data leak sites.
Warlock also seems to have potential ties to Black Basta, a prolific ransomware group that stopped publishing victims in early 2025. While connection remains unconfirmed, similarities in tactics, negotiation styles, and victimology hint at a possible offshoot or rebrand.
Global Impact and Response
Scale of Compromise
The latest number of compromises is over 400 victims, as The Register reports. Most of the affected systems are located in the US and Germany. While more than 80 victims were known until last weekend, the number soon rose to 100, including the US Nuclear Weapons Agency, according to Bloomberg.
Regulatory and Government Response
CISA has added one new vulnerability to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. See CISA’s Alert Microsoft Releases Guidance on Exploitation of SharePoint Vulnerability (CVE-2025-53770) for more information and to apply the recommended mitigations.
CISA is aware of active exploitation of a spoofing and RCE vulnerability chain involving CVE-2025-49706 and CVE-2025-49704, enabling unauthorized access to on-premise SharePoint servers.
Industry Response
On July 21, 2025, Cloudflare deployed our emergency WAF Managed Rules to patch the vulnerability, meaning every customer using the Cloudflare Managed Ruleset will automatically be protected from this critical SharePoint vulnerability.
Strategic Implications and Future Outlook
The Hybrid Threat Evolution
Warlock represents a concerning evolution in the cyber threat landscape, where the traditional boundaries between state-sponsored espionage and financially motivated cybercrime continue to blur. This raises the possibility that Chinese nation-state actors may be purchasing access to ransomware tools or services from cybercriminal marketplaces, using them for both sanctioned operations and unsanctioned personal profit.
Critical Infrastructure Vulnerabilities
The targeting of major telecommunications providers like Colt and Orange demonstrates Warlock’s strategic focus on critical infrastructure. The incident demonstrates the imperative of rapid vulnerability management and cross-sector threat intelligence sharing.
The RaaS Model’s Continued Evolution
“In recent years, this kind of rapid escalation has become typical for ransomware groups trying to establish credibility,” Benjamin Zigh, director of product management at Trend Micro, tells Dark Reading. “Warlock’s aggressive branding, including its flashy debut on underground forums, is designed to attract affiliates and intimidate victims. The ransomware-as-a-service (RaaS) model thrives on reputation, and new groups often pursue high-profile targets or exploit trending vulnerabilities (like ToolShell in this case) to gain visibility and momentum.”
Mitigation and Defense Strategies
Immediate Actions
Organizations running on-premises SharePoint servers should immediately:
- Apply Security Updates: Apply the latest security updates linked above.
- Rotate Machine Keys: Rotate ASP.NET machine keys, then after applying Microsoft’s security update, rotate ASP.NET machine keys again, and restart the IIS web server.
- Enable AMSI: Ensure the Antimalware Scan Interface is turned on and configured correctly
Detection and Monitoring
Look for the creation of spinstall0.aspx, which indicates successful post-exploitation of CVE-2025-53770.
Organizations should monitor for:
- Unusual ASPX files in SharePoint web roots
- Outbound HTTPS traffic to unfamiliar cloud storage domains
- Credential dumping activity (lsass.exe minidumps)
Long-term Security Posture
“Organizations should actively monitor suspicious account activity or policy changes, restrict access to administrative shares, and promptly flag abnormal script or command executions. They should also detect and respond to attempts to disable security tools, block unauthorized service or driver installations, and identify signs of lateral movement,” Trend Micro urged.
Conclusion: A New Chapter in Cyber Warfare
The Warlock ransomware campaign represents more than just another cybersecurity incident—it signals a fundamental shift in the global threat landscape where nation-state capabilities, criminal motivations, and critical infrastructure vulnerabilities converge in unprecedented ways.
Warlock represents a fast-maturing ransomware operation distinguished by its reliance on high-impact zero-day exploits, data theft, and stealthy web shell deployment. Though attribution centers on the Storm-2603 actor, broader motivations and sponsor affiliations remain unconfirmed. The group has already demonstrated the ability to disrupt high-profile and well-defended targets with precision, making it one of the most closely watched ransomware threats of 2025.
The implications extend far beyond the immediate victims. The successful targeting of telecommunications giants like Colt and Orange demonstrates that critical infrastructure remains vulnerable to sophisticated threat actors who can rapidly weaponize zero-day vulnerabilities and monetize stolen data through innovative auction mechanisms.
As we move forward, organizations must recognize that traditional defense strategies are insufficient against hybrid threats like Warlock. The rapid evolution from vulnerability disclosure to weaponization, the blending of state and criminal capabilities, and the increasing sophistication of data monetization strategies all point to a new era in cybersecurity where proactive defense, rapid response, and international cooperation are not just recommended—they are essential for survival in the digital ecosystem of 2025.
The Warlock campaign serves as a stark reminder that in today’s interconnected world, a vulnerability in one organization’s SharePoint server can become a gateway to global chaos, and the next “Lamborghini” promised on a cybercrime forum might just be funded by your organization’s data.
This analysis is based on intelligence gathered from multiple cybersecurity firms, government agencies, and threat intelligence platforms as of August 2025. The threat landscape continues to evolve rapidly, and organizations should consult the latest advisories from Microsoft, CISA, and their cybersecurity providers for the most current mitigation guidance.