8,809 institutions. ~275 million records. One freemium tier.
On or around April 30, 2026, a threat actor walked into the platform that roughly 41% of North American higher education runs on — and walked out with names, institutional email addresses, student ID numbers, and a substantial volume of private messages exchanged between students, teachers, and advisors.
The vector wasn’t a sophisticated zero-day. It wasn’t a nation-state APT. It was a freemium account program — Canvas Free-For-Teacher (FFT) — that was provisioned with low-friction onboarding, ran on the same production multi-tenant infrastructure as paid institutional Canvas tenants, and had a verification gap large enough for ShinyHunters to drive through twice in eight months.
This is not a Canvas story. This is an LMS supply chain story, and every CISO, superintendent, IT director, and general counsel in education needs to read it that way.
The Timeline, As Confirmed
What we know publicly, sourced to Instructure’s own status disclosures, ShinyHunters’ ransom notes, and reporting across multiple outlets:
April 30, 2026 — Initial unauthorized access begins. The exposure window ran from April 30 to May 7.
May 1 — Instructure publicly discloses “a cybersecurity incident perpetrated by a criminal threat actor.” Canvas Data 2 and Canvas Beta are taken offline.
May 2 — Instructure claims the situation is “contained.” Confirmed exposed data fields: names, email addresses, student ID numbers, messages among users.
May 3 — ShinyHunters publishes a ransom note via Ransomware.live claiming 275 million records and 3.65 TB of stolen data, with a May 6 deadline for negotiation.
May 7 (~1:20 PM PDT) — Canvas login pages across the world are replaced with a ShinyHunters defacement message: “SHINYHUNTERS rooting your systems since ‘19 ;) ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some ‘security patches.’” New deadline: end of day May 12.
May 8 — Instructure restores service after taking Canvas, Canvas Beta, and Canvas Test offline. The company confirms the exploit was tied to an issue in the Free-For-Teacher account program and announces it is permanently shutting down FFT.
May 12 — Instructure confirms it paid a ransom and reached an agreement with ShinyHunters, receiving “digital confirmation of data destruction” hours before the hackers’ final deadline. The amount was never disclosed.
As of May 14 — Forensic analysis is ongoing. CrowdStrike has been engaged. A separate e-discovery vendor has been brought in to conduct a large-scale review of which records belong to which institutions — a process Instructure has said could take weeks.
For affected schools, that last point is the operational nightmare. Schools should expect to wait weeks to months for Instructure to issue a final post-incident report and individualized scope letters identifying which records belonging to their institution were accessed. Notification obligations under state law and FERPA do not wait politely for vendor forensics.
The Scope: Reading the Map
The visualization circulating on LinkedIn from Edtech Insiders maps the leaked customer list. The numbers it shows are the floor, not the ceiling:
- 8,809 institutions named in the leaked customer list
- 7,400 U.S. institutions, all 50 states + D.C. + Puerto Rico
- 1,407 international accounts across 60+ countries
- Top affected U.S. states: California (1,040), Texas (764), Florida (430), Virginia (371), North Carolina (304)
- Top affected international: Argentina (388), Australia (138), United Kingdom (125)
Threat intelligence breakdown: 2,514 higher education institutions — among them all eight Ivy League universities, major state university systems, and internationally recognized institutions including Oxford, Cambridge, NUS, and the University of Melbourne — and 1,616 K–12 school districts, including large urban systems such as Clark County (Las Vegas), Houston ISD, and Miami-Dade.
The K-12 roster alone — LAUSD, Chicago Public Schools, Miami-Dade, Clark County, Broward, Houston ISD, Fairfax, Gwinnett, Wake County, Dallas ISD, Boston Public Schools, the entire Hawaii Department of Education — represents millions of minor children. That single fact is the regulatory hinge this entire incident turns on.
What Actually Got Stolen
Instructure has confirmed: names, institutional email addresses, student ID numbers, and messages exchanged between Canvas users — students to students, students to teachers, students to advisors.
What Instructure says was not compromised: passwords, dates of birth, government identifiers, financial information, and core coursework data like submissions and grades.
That sounds reassuring until you sit with what “messages among users” actually contains in an LMS context. Canvas isn’t just an assignment-drop tool. It is the substrate for medical accommodation requests — students disclosing disabilities, mental health conditions, and chronic illnesses to disability services offices. Private advisor conversations about financial hardship, family circumstances, immigration status, and mental health crises. Title IX adjacent communications. K-12 parent-teacher messaging including pediatric medical information, behavioral concerns, and custody situations. Faculty-to-faculty discussions about specific students’ performance or suspected misconduct.
The compromise of name + institutional email + student ID + the content of private messages is, for spear-phishing purposes, significantly more dangerous than a stolen password file. Passwords get rotated in 24 hours. The fact that a specific student disclosed a mental health diagnosis to a specific advisor in a specific course in spring 2024 doesn’t get rotated.
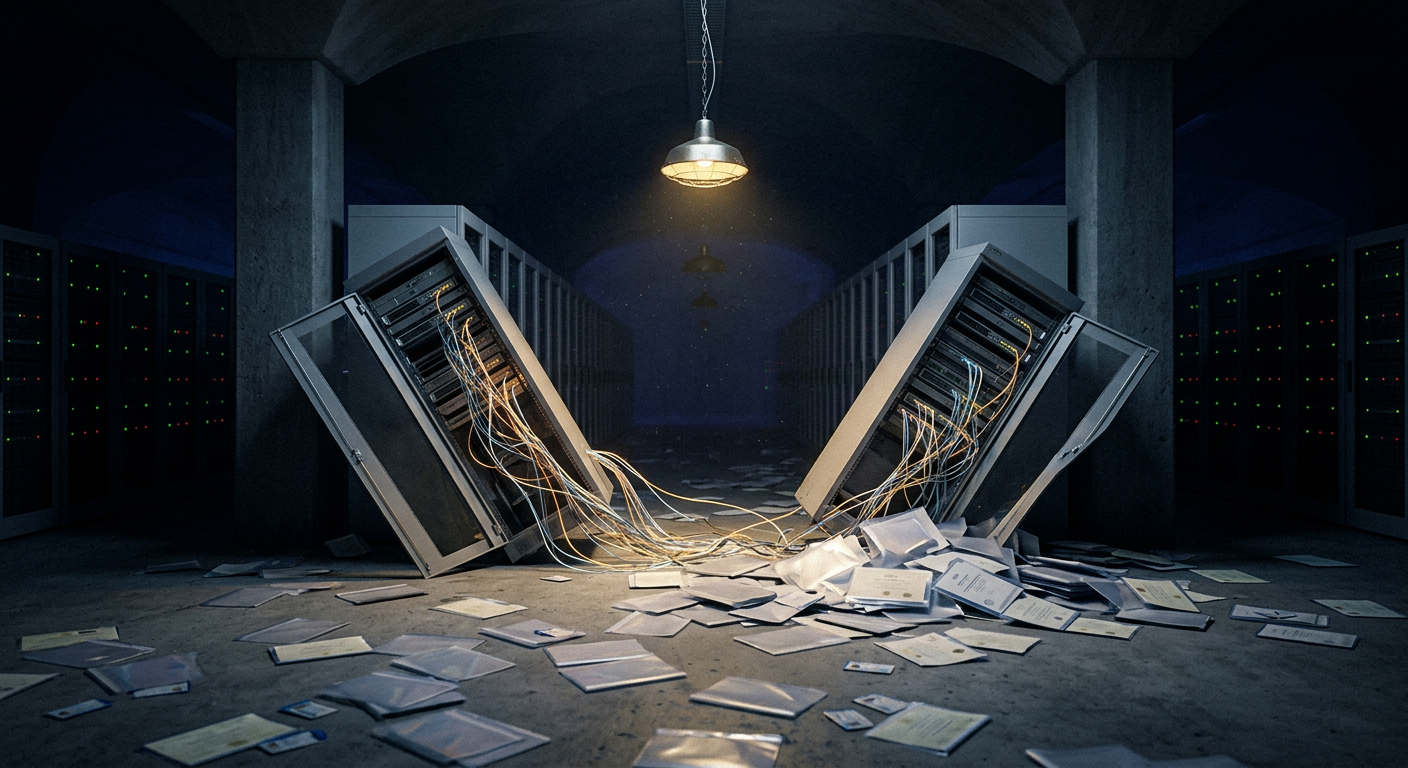
The Architectural Failure: Freemium Tier as Production Attack Surface
This is the part of the story the headlines have undersold.
Canvas Free-For-Teacher accounts were designed to let any educator — without institutional affiliation, without paid contracts, without verification — spin up a Canvas tenant for their own classroom. Low friction was a feature, not a bug. FFT accounts were production Canvas tenants with low-friction onboarding and no institutional verification, running on the same multi-tenant infrastructure as paid institutional environments.
That’s the architectural problem in one sentence.
Multi-tenant SaaS depends on logical isolation: row-level scoping, application-layer permissions, API authorization boundaries that prevent one tenant from reading another’s data. Those controls work right up until the moment one tenant class has materially weaker identity verification than another. When attackers exploited the support ticket pathway in FFT, the fundamental isolation model failed — granting unauthorized lateral access to production course data across paying institutional tenants.
The lesson generalizes well beyond Canvas: if your freemium tier and your enterprise tier share back-end infrastructure, your enterprise customers are inheriting the freemium tier’s threat model whether they know it or not. Every SaaS PM in EdTech should reread their own onboarding flows tonight.
ShinyHunters and the Supply Chain Pattern
This is not ShinyHunters’ first move against Instructure. The same group compromised Instructure’s Salesforce environment in 2025 — part of the broader ShinyHunters enterprise vishing and Salesforce campaign we’ve been tracking all year. Their documented approach is consistently to exploit a trusted third-party integration or lower-trust entry point to reach a higher-value target.
The thesis ShinyHunters is operating on is simple and correct: attack one platform that 9,000 institutions sit on top of rather than 9,000 institutions one at a time. Instead of targeting individual campuses, they’re moving up the data supply chain to the platforms that sit underneath thousands of institutions at once.
That is the structural reality the EdTech sector is now operating in. The procurement decision to consolidate onto a single vendor for cost and integration reasons is, in 2026, also a decision to share that vendor’s threat model with every peer institution on the same platform. We covered the full scope of ShinyHunters’ operational evolution — from Ticketmaster (560 million records) through AT&T, Santander, and multiple Ivy League institutions — in our group profile published last year.
The Regulatory Landscape: FERPA, COPPA, HIPAA, GDPR, and ~130 State Statutes
This is where the bill comes due — and it does not come due for Instructure. It comes due for the schools.
FERPA requires educational institutions to notify students when their education records have been improperly disclosed. ComplianceHub.Wiki’s state breach notification guide covers the full patchwork of state-level deadlines that layer on top of FERPA’s federal floor. The triggering event is the disclosure, not the vendor’s remediation. Instructure’s public confirmation means the clock was already running for every institution using Canvas as of May 1.
COPPA is the most severe exposure for K-12. The FTC’s updated rule (effective April 22, 2026) applies to under-13 user data and carries per-child penalties — ComplianceHub.Wiki broke down exactly what operators needed in place before that deadline. The math on a per-child penalty across the LAUSD, Chicago Public Schools, and Miami-Dade student populations is not a calculation anyone at Instructure wants to surface publicly.
HIPAA is in play for medical institutions on the list — including Weill Cornell Medical College and the University of Nebraska Medical Center — that used Canvas for clinical training programs. PHI exposure depends on what flowed through course messaging.
State statutes: Because Canvas serves K–12 districts, colleges, universities, and education ministries, the breach implicates roughly 130 state student-privacy statutes in addition to federal frameworks. Most of these place the notification burden on the institution rather than the vendor. Schools have to issue notice to their communities using data they do not yet have, on regulatory clocks that are already running.
GDPR Article 33/34 obligations are in play for European institutions and any U.S. institution holding EU-resident student records. Australia’s Notifiable Data Breaches scheme covers the 138 named Australian institutions. The UK ICO is active given 125 named UK institutions.
For Affected School Leaders: What to Do This Week
If your institution is on the leaked list — and the realistic answer for any North American higher ed institution or large K-12 district is probably yes — you are not waiting for forensic certainty before acting.
Before diving into the checklist: if your institution hasn’t formally assessed its security posture recently, school.secureiot.house offers a free 10-minute assessment across all nine domains — physical security, cybersecurity, IoT and smart campus, data privacy, FERPA/COPPA compliance, incident response, and more. It’s a useful baseline for understanding where the gaps are before the next vendor breach lands.
Engage cybersecurity counsel before anything else. Privilege matters. Communications produced after engagement are protected in ways that pre-engagement work product is not.
Notify your cyber insurance carrier. Notification triggers in most policies are awareness, not confirmation. The clock started May 1.
Stand up an IR team with explicit roles — communications, legal, IT, compliance, with one person owning the parent/student/faculty message.
Issue informal community notification. A short, plain-language note from a named leader explaining what is known, what is not, and what the institution is doing. Schools should not wait for Instructure’s final scope letter to communicate with their communities.
Rotate every Canvas API token and integration credential. Anything that talked to Canvas via API in the April 30 – May 7 window should be considered potentially exposed.
Push Instructure for a tenant-specific scope letter with a committed date. “We’re still investigating” is not an acceptable final answer.
Document everything. Every decision, every meeting, every external communication. State AG inquiries are coming.
Over the next 30 days: Re-read your Data Processing Agreement with Instructure — specifically incident response timeline obligations, indemnification, and audit rights. Audit your data minimization posture. Assess your spear-phishing exposure and push out training. Engage with your state AG proactively if your state has a strong student privacy framework — California, Illinois, New York, Colorado, and Virginia all have meaningful leverage here, and proactive engagement is treated very differently from reactive engagement. ComplianceHub.Wiki’s AG notification directory has direct portal links for every state.
For K-12 specifically: plan parent notification language in plain English and Spanish, coordinate with district legal counsel on COPPA-specific notice for under-13 children, and brief your school board in writing, on the record.
For Parents and Students: The Realistic Threat Model
The most likely thing that happens to you is a phishing attempt that uses real institutional context — a fake email appearing to come from your child’s school, your registrar, your academic advisor, or your university IT helpdesk, referencing real course names, real instructor names, real recent communications. The data set ShinyHunters had gives attackers everything they need to make these look genuine.
Treat this as a phishing alert, not a panic moment. Freeze your child’s credit — yes, minors have credit reports, and Equifax, Experian, and TransUnion all let you freeze a minor’s file for free. Reset passwords anywhere your family reused the school portal password. And ask the institution one direct question: what student data fields were in the leaked database, and when will we receive formal notice? If the answer is vague, escalate to the school board, the provost’s office, or your state AG.
The FBI has explicitly warned that scammers will piggyback on this breach to extort individuals who weren’t actually exposed. Be skeptical of any unsolicited “we have your data” outreach.
The Bigger Point: EdTech Procurement Is Downstream of Trust
The Canvas breach is significant not because the vulnerability was sophisticated — it almost certainly wasn’t — but because of where in the stack it happened.
A breach at the LMS layer, where assignments, advising conversations, accommodation requests, and parent-teacher messages all hang off the same plumbing, is not a Canvas problem. It is a sector problem. The EdTech industry has spent a decade consolidating onto a small number of platforms that sit underneath everything else: PowerSchool, Illuminate, Instructure, Blackboard. Each consolidation made the procurement decision simpler and the blast radius larger.
The next breach is already being researched somewhere. The right question for every superintendent, CISO, provost, and board member is not “are we on the affected list?” It is:
- Do we have an incident response plan that contemplates a vendor-side breach we cannot directly remediate?
- Do our DPAs actually obligate vendors to give us tenant-specific scope information in days, not months?
- Are we collecting student data we don’t actually need, just because the platform makes it easy?
- Do we have a parent/student/faculty communication template ready to deploy in the next 24 hours, not the next 24 days?
The next conference panel cannot be about AI personalization in the classroom if we haven’t fixed the data hygiene of the platforms underneath. The Canvas breach is the warning shot. The institutions that treat it that way will be in materially better shape when the next one lands.
And there will be a next one.
Listen: The EdTech Supply Chain Collapse
Further reading on this incident:
- ShinyHunters Breaches Instructure: 275 Million Students’ Canvas Data Stolen — the initial breach analysis
- Instructure Paid the Ransom: ShinyHunters Claims Data Destruction — the ransom payment outcome
- PowerSchool to Canvas: The 18-Month EdTech Supply Chain Collapse — the 18-month pattern analysis
- ShinyHunters’ Enterprise Salesforce Vishing Campaign — the broader campaign context
- U.S. State Data Breach Notification Compliance Guide — ComplianceHub.Wiki
- COPPA April 22 Deadline: What Operators Must Have in Place — ComplianceHub.Wiki
- State AG & Consumer Protection Notification Portal Directory — ComplianceHub.Wiki
- Privacy & Cybersecurity Articles — MyPrivacy.Blog
- Free School Security Assessment Tool — school.secureiot.house
- Smart City & Connected Infrastructure Cybersecurity Assessment — smartcity.secureiot.house
Sources
- Instructure status page and official disclosures (May 1–12, 2026)
- ShinyHunters ransom note published via Ransomware.live (May 3, 2026)
- Inside Higher Ed: “Pay or Leak” coverage
- CNN, NPR, TIME, Dark Reading breach coverage
- Trend Micro, Bitdefender, Dataminr threat intelligence briefs
- Wikipedia: 2026 Canvas security incident
Breached.Company covers state-sponsored cyber and hybrid threats, breach disclosures, and signals intelligence for the security community. For threat intelligence retainers and vCISO consulting, CISO Marketplace connects you with vetted advisors.