Eighteen months. Two breaches. Roughly 350 million combined records spanning K-12, higher education, alumni, donors, faculty, and staff. Different attackers, different vectors, but the same underlying architectural failure: a single vendor compromise cascading across thousands of institutions because the data was consolidated onto shared infrastructure in the first place.
The May 2026 Canvas breach — covered in our main incident analysis and supply chain framing piece — is not an isolated incident. It is the predictable next chapter of a story that began with the PowerSchool disclosure in January 2025, compounded by 18 months of Ivy League and R1 university compromises through Oracle EBS, Salesforce, and vishing campaigns.
This piece compares the two anchor incidents head-to-head, traces the through-line connecting them to the broader university breach wave, and argues that the education sector’s vendor consolidation strategy is now structurally incompatible with the regulatory frameworks that govern student data.
The Two Anchor Breaches: A Side-by-Side
| PowerSchool (Dec 2024) | Canvas / Instructure (May 2026) | |
|---|---|---|
| Disclosed | January 2025 | May 1, 2026 |
| Records affected | ~72M (62M students, 9.5M educators) | ~275M claimed |
| Institutions affected | 18,000+ schools | 8,809 schools, 50+ countries |
| Market share | ~75% of N. American K-12 SIS | ~41% of N. American higher ed LMS |
| Threat actor | Matthew Lane (solo, age 19) | ShinyHunters (organized group) |
| Initial access vector | Stolen contractor credentials | Free-For-Teacher account program |
| Root architectural flaw | No MFA on customer support portal | Free tier sharing production infra with paid tier |
| Dwell time | 9 days undetected | 7 days (Apr 30 → May 7) |
| Data exposed | Names, SSNs (25% of records), special ed/IEP, medical alerts, custody, mental health, discipline | Names, emails, student IDs, private messages |
| Ransom paid? | Yes — then re-extortion continued for months | Yes — undisclosed amount, May 12 |
| Outcome for attacker | 4 years federal prison (Oct 2025) | Still operating |
The differences look significant. They aren’t. Both attacks succeeded because a single vendor operated a piece of infrastructure that thousands of schools depended on without applying enterprise-grade controls to one critical edge. For PowerSchool, that edge was the customer support portal. For Canvas, it was the Free-For-Teacher program. Different edge, same lesson.
We analyzed PowerSchool’s architectural failure at length in When the Cloud Falls: Third-Party Dependencies and the New Definition of Critical Infrastructure — PowerSchool’s PowerSource customer support portal stored data on tens of millions of children’s Social Security numbers and medical records protected by single-factor authentication. A stolen contractor credential walked right in. A vendor that almost certainly passed whatever risk assessments its customers performed.
For Canvas, the equivalent weak edge was the Free-For-Teacher program: production Canvas tenants with low-friction onboarding and no institutional verification, running on the same multi-tenant infrastructure as paying institutional environments. Instructure confirmed that attackers exploited a vulnerability in the support ticket pathway of the FFT environment. Different edge, same lesson: a weaker trust boundary inside a multi-tenant platform becomes a lateral movement vector into the paid customer base.
What Each Breach Tells Us That the Other Doesn’t
PowerSchool: The Identity Disaster
The PowerSchool breach is the more sensitive of the two on a per-record basis. The compromised data included names and addresses, Social Security numbers (approximately 25% of affected students), special education status including IEP and 504 designations, mental health conditions and therapy records, disciplinary records, parental restraining orders and custody arrangements, and medical alerts including anxiety disorders, medications, and health conditions.
This is the kind of dataset that fuels lifelong identity fraud. Children’s Social Security numbers are particularly valuable precisely because the fraud often isn’t discovered for years — until the child applies for student loans, a first apartment, or a first credit card. Matthew Lane, sentenced to four years in federal prison in October 2025, didn’t need to be sophisticated. The contractor credential gave him everything.
PowerSchool also revealed something important about ransom dynamics in EdTech: paying does not make the data go away. PowerSchool paid and received video purportedly showing data deletion. Months later, multiple school districts received separate extortion demands referencing the same data, suggesting Lane either resold the data or shared it before the “deletion.” This is the structural problem with extortion as a control: there is no enforcement mechanism.
Canvas: The Communications Disaster
The Canvas breach is the more behaviorally dangerous of the two. It does not include Social Security numbers, dates of birth, or financial information. What it includes is the content of private messages exchanged inside Canvas: student-to-advisor mental health disclosures, medical accommodation requests, Title IX adjacent communications, K-12 parent-teacher messaging about specific children, and faculty-to-faculty discussions about individual students.
The PowerSchool breach gave attackers identity-grade structured data. The Canvas breach gives attackers context — the unstructured narrative content that makes spear-phishing devastatingly effective. A stolen SSN gets a credit freeze applied. A stolen private message disclosing a depression diagnosis to an academic advisor cannot be un-stolen, and it can be weaponized for extortion or social engineering indefinitely.
Taken together, the two breaches represent the two halves of a complete attack toolkit against the U.S. education sector. PowerSchool delivered structured identity data. Canvas delivered unstructured behavioral context. An attacker willing to correlate both datasets has something genuinely unprecedented: real identities plus real disclosures plus real institutional context for a substantial portion of the U.S. student population.
The 18-Month Higher Ed Breach Wave: Context, Not Coincidence
PowerSchool and Canvas are the two largest education-sector incidents of this period, but they are bracketed by a dense cluster of compromises at individual institutions following consistent patterns.
The Clop / Oracle EBS Campaign
In mid-2025, the Clop ransomware group weaponized CVE-2025-61882, a 9.8 CVSS unauthenticated remote code execution vulnerability in Oracle E-Business Suite — we analyzed the full campaign in The Perfect Supply Chain Storm and the Oracle EBS zero-day technical breakdown. Confirmed higher ed victims included University of Phoenix (3.5 million records) and Baker University, Harvard (1.3 TB), and Dartmouth (35,000+ records).
Oracle EBS is the financial backbone for many universities — tuition processing, payroll, vendor payments, student aid disbursements. One CVE in one product line cascaded across the entire higher ed sector simultaneously. Same supply chain failure pattern as PowerSchool and Canvas, different vendor.
The ShinyHunters Vishing Campaign
The same group behind the Canvas breach has been working higher ed via voice phishing for at least 18 months. We covered the Ivy League wave in detail in Hackers Strike US Ivy League Schools Already Under Political Pressure and the Harvard vishing incident. Confirmed targets include Columbia (870,000 records), Princeton, Harvard Alumni Affairs and Development (November 2025), and the University of Pennsylvania.
The Penn breach was structurally significant: attackers compromised a single PennKey account and exported data on 1.2 million students, alumni, and donors from Salesforce, SharePoint, Box, Qlikview, and Marketing Cloud simultaneously. No zero-day required. No sophisticated malware. A compromised credential, and every SaaS integration that credential touched became accessible.
The “Payroll Pirate” Campaign
Microsoft Threat Intelligence has tracked Storm-2657, a financially motivated cluster running phishing campaigns against university Workday profiles since March 2025. The goal: redirect salary payments to attacker-controlled accounts via compromised HR systems. Different objective from data theft, same operational target — the SaaS layer that universities depend on for HR, finance, and student services.
The Through-Line
The 18-month picture breaks down cleanly by sector layer:
K-12: PowerSchool → broad downstream extortion of districts → Canvas K-12 component.
Higher ed administrative and donor data: Clop/Oracle EBS at Phoenix, Harvard, Dartmouth, Baker → vishing at Columbia, Princeton, Harvard AAD, Penn → Workday/Payroll Pirate at 25 universities.
Higher ed academic data: Canvas / Instructure.
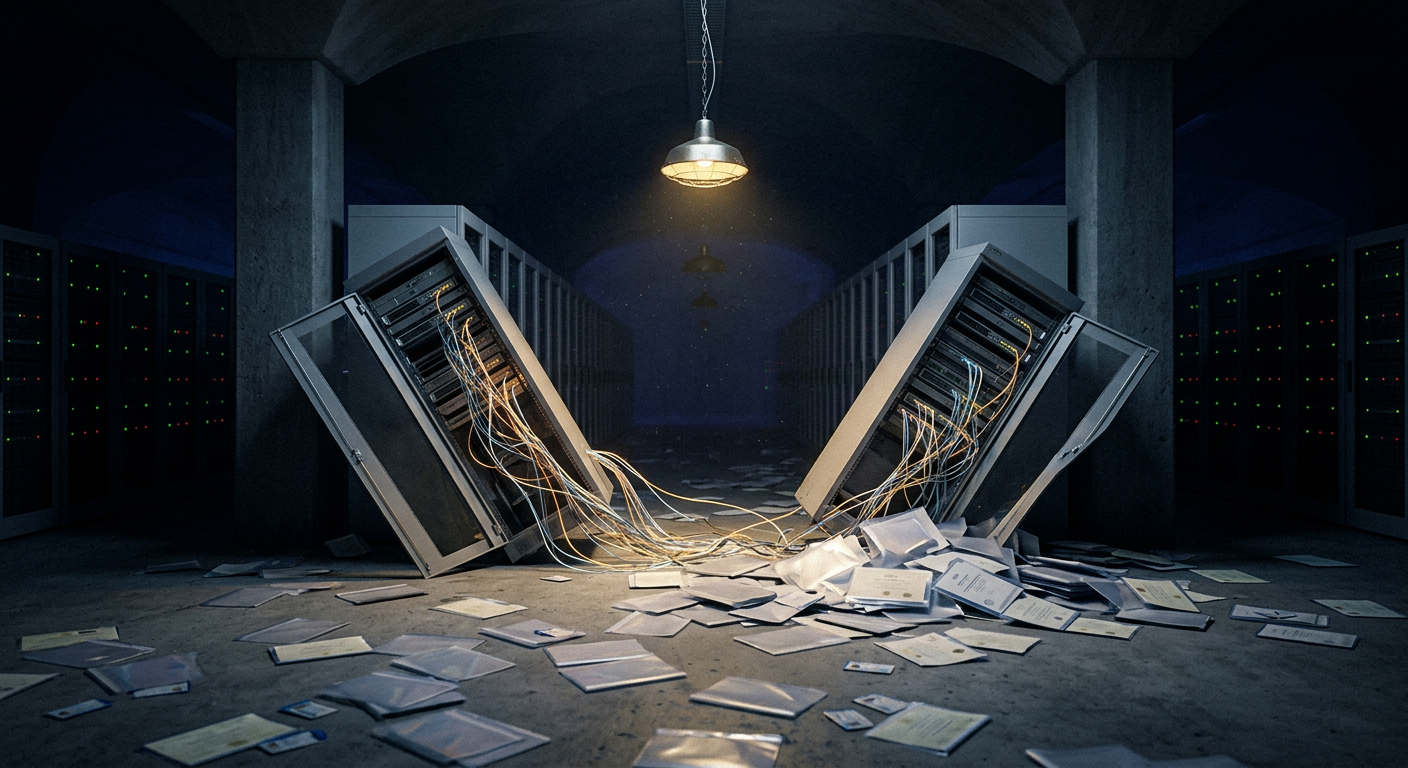
Every layer of the education sector’s technology stack has been compromised at scale in the last 18 months. The constant is not the attacker, the vector, or the vendor — it’s the architectural reality that thousands of institutions now sit on top of a small number of platforms that were never designed to be the central data custodians for an entire sector.
The Pattern That Connects All of It
Six structural features make this entire wave one story rather than a collection of bad luck.
Vendor consolidation has concentrated blast radius. PowerSchool has roughly 75% K-12 SIS market share. Canvas has 41% higher ed LMS share. Oracle EBS sits underneath most R1 university financial operations. When procurement chooses “one vendor for everyone,” a single breach hits everyone.
The weakest tier defines the security posture. PowerSchool’s enterprise customers inherited the security posture of an unmaintained support portal. Canvas’s paying institutional customers inherited the security posture of an unverified free-teacher program. Multi-tenant SaaS without per-tier hardening is structurally fragile in ways that most enterprise procurement processes are not equipped to detect.
Notification burden falls on the regulated entity, not the technical failure point. Schools owe notice to students, parents, regulators, and AGs. Vendors owe ambiguous “without undue delay” obligations under most DPAs. The mismatch between where the technical failure happens and where the legal liability lands is the central feature of the EdTech threat landscape in 2026. ComplianceHub.Wiki’s comprehensive state notification guide and AG portal directory are the practical starting point for institutions mapping their obligations right now.
Forensic timelines outrun regulatory timelines. Instructure has publicly stated that tenant-specific scope letters will take “some weeks” to produce. PowerSchool’s full scope disclosure took months. Meanwhile, state notification deadlines run 30–60 days, GDPR runs 72 hours, and state AGs are already active. Schools are required to notify before they know what to notify about.
Paying ransoms does not contain the damage. PowerSchool paid. Multiple districts were re-extorted independently in the months following. The Canvas breach unfolded publicly precisely because ShinyHunters had no commercial incentive to honor a settlement — they had burned the relationship with Instructure twice: first in the 2025 Salesforce vishing campaign, then with Canvas in 2026, with the May 7 defacement explicitly calling out Instructure’s failed “security patches.”
The same threat actor returns. ShinyHunters first compromised Instructure’s Salesforce environment in 2025, then came back for Canvas in 2026. We documented the full arc of the group’s evolution — Ticketmaster (560M records), AT&T, Santander, multiple Ivy League institutions — in our ShinyHunters group profile. The lesson: successful extortion campaigns self-reinforce. The attacker returns to the same victim because the second compromise is easier than the first.
What This Means for Vendor Risk Management
Most school district and university vendor risk programs are built for a 2015 threat model: SOC 2 reliance, annual questionnaires, cyber insurance, a signed DPA. That model has now been broken in public three times in 18 months — PowerSchool, Oracle EBS, Canvas — and any institution still operating it as a primary control is operating on luck.
The post-Canvas vendor risk posture for EdTech should include, at minimum:
Notification SLAs measured in hours, not “without undue delay.” 24–48 hours from vendor awareness, with defined contact methods and escalation paths.
Contractual tenant-scope SLAs. “Preliminary scope within 30 days, final scope within 90 days” is far better than the typical open-ended timeline Instructure is currently operating under.
Multi-tenant architecture disclosure obligations. Vendors should be contractually required to disclose tier-sharing, free-tier programs, and any condition where a less-privileged tenant class shares infrastructure with paying customers.
Sub-processor change notification rights. When CrowdStrike, e-discovery vendors, or any other party begins processing your data, you need advance notice and meaningful opt-out rights.
Indemnification sized to realistic breach cost, not annual fees. A $50K SaaS contract should not cap indemnification at $50K when realistic breach cost is $2–5M per district.
Data minimization as contract term. Vendors should be obligated to delete data fields the institution does not actively use — not merely permitted to retain everything indefinitely.
Audit rights that are real, not theoretical. SOC 2 reliance is no longer adequate post-PowerSchool, post-Canvas. Period.
Institutions looking for a structured starting point can run the free security assessment at school.secureiot.house — it covers all nine security domains including third-party vendor management, IoT and smart campus infrastructure, data privacy, and FERPA/COPPA compliance readiness in under 10 minutes. For institutions operating connected campus infrastructure, smartcity.secureiot.house provides a parallel assessment framework for smart city and connected-infrastructure security posture.
What’s Coming Next
The honest forecast: the next breach is already being researched somewhere right now. The consolidation pattern hasn’t changed. The architectural mistakes haven’t been corrected at most vendors. The attacker economics — low operational cost to extract data on tens of millions of records monetizable for years — still strongly favor the attacker.
The next likely target categories: the remaining major LMS platforms (Blackboard, D2L Brightspace), student information systems beyond PowerSchool (Infinite Campus, Skyward), university CRM and advancement platforms (Salesforce Education Cloud, Slate, Blackbaud — Penn already showed the playbook), the financial aid layer (Heartland ECSI, Workday Student, Ellucian), and EdTech assessment platforms (Pearson VUE, ETS, College Board).
The structural answer is not “find a more secure vendor.” There may not be one at this scale. The structural answer is for the institutions, regulators, and procurement bodies that drove the consolidation in the first place to reckon with what they bought: a small number of single points of failure for the educational data of an entire continent.
PowerSchool was the warning. Canvas was the confirmation. Whatever comes next is the consequence.
Listen: The EdTech Supply Chain Collapse
Related coverage on this incident:
- ShinyHunters Breaches Instructure: 275 Million Students’ Canvas Data Stolen
- The Canvas Breach Is an LMS Supply Chain Failure, Not a School Problem
- Instructure Paid the Ransom: ShinyHunters Claims Data Destruction
- ShinyHunters’ Enterprise Salesforce Vishing Campaign
- When Billionaires Become the Breach: Harvard’s Donor Database
- Penn University: 1.2M Records and 18 Class Action Lawsuits
- When the Cloud Falls: Third-Party Dependencies and Critical Infrastructure
- The Perfect Supply Chain Storm: Cl0p’s Oracle Rampage
Compliance and privacy resources:
- U.S. State Data Breach Notification Compliance Guide — ComplianceHub.Wiki
- COPPA April 22 Deadline: What Operators Must Have in Place — ComplianceHub.Wiki
- State AG & Consumer Protection Notification Portal Directory — ComplianceHub.Wiki
- Privacy & Cybersecurity Articles — MyPrivacy.Blog
- Free School Security Assessment Tool — school.secureiot.house
- Smart City & Connected Infrastructure Cybersecurity Assessment — smartcity.secureiot.house
Breached.Company covers state-sponsored cyber and hybrid threats, breach disclosures, and signals intelligence for the security community. For threat intelligence retainers and vCISO consulting, CISO Marketplace connects you with vetted advisors.