March 4, 2025 — In one of the most sweeping international cybercrime enforcement actions of the year, the Federal Bureau of Investigation, Europol, and law enforcement agencies spanning 14 countries have dismantled LeakBase — a massive open-web forum where cybercriminals bought, sold, and traded stolen data from breaches targeting American corporations, individuals, and entities worldwide.
The operation, dubbed Operation Leak, unfolded in two synchronized phases across March 3–4, and the results were decisive: the forum is gone, its domains seized, its data in the hands of investigators, and dozens of its most active users now squarely in the crosshairs of international law enforcement.





What Was LeakBase?
For those outside the cybercriminal underground, LeakBase operated as a clearinghouse for stolen credentials, financial data, and sensitive personal information harvested from high-profile data breaches. The forum had over 142,000 members and more than 215,000 messages between members, and maintained an enormous, continuously updated archive of hacked databases — including hundreds of millions of account credentials.
Unlike some of its darker-web counterparts, LeakBase operated on the open web and in English, making it broadly accessible. But within the cybercriminal community, it was particularly well-known as a destination for Eastern European threat actors — a distinction that made it a different beast from competitors like the now-defunct Breached forum. Where Breached catered to a more globally diverse English-speaking hacker crowd, LeakBase had strong roots in Eastern European cybercrime circles, with its infrastructure and user base reflecting that demographic.
The forum allowed users to sell information from stolen databases, including data illegally obtained from U.S. corporations and individuals, offering credit and debit card numbers, banking account and routing information, usernames and associated passwords to facilitate account takeovers, as well as other sensitive business and personally identifiable information.
A Two-Phase Takedown
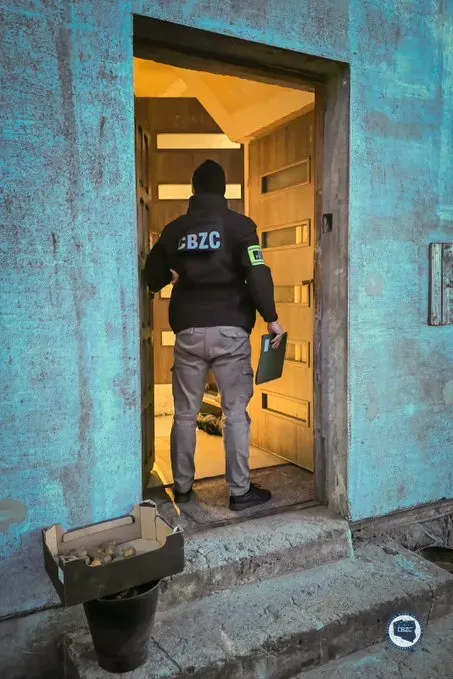
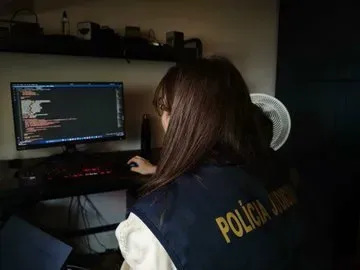
The operation followed a deliberate, coordinated playbook. On March 3, law enforcement agencies across multiple jurisdictions launched simultaneous kinetic enforcement actions — boots on the ground, doors knocked, and in some cases, knocked in.
Law enforcement executed search warrants, arrests, and conducted interviews in the United States, Australia, Belgium, Poland, Portugal, Romania, Spain, and the United Kingdom. The images released by Poland’s CBZC (Central Bureau for Combating Cybercrime) capture the operational tempo: officers in tactical gear entering residences, suspects being interviewed at laptops, and digital forensics analysts working through seized devices in real time.
Around 100 enforcement actions were conducted worldwide, with measures specifically targeting 37 of the most active users of the platform — the heavy hitters whose activity drove the most value to the criminal marketplace.
Then, on March 4, authorities moved to the technical disruption phase. The United States and other countries shut down LeakBase, seized its data and two of the domains used by the forum, and posted seizure banners on the LeakBase sites. The domain registration data tells the story cleanly: leakbase.la now resolves to nameservers at ns1.fbi.seized.gov and ns2.fbi.seized.gov. Anyone who visits the site today sees the unmistakable blue seizure splash page bearing the seals of the FBI, Europol, the NCA, Politie, AFP, and a dozen other agencies.
New LeakBase domain: https://t.co/dNwTuDrYrE pic.twitter.com/qH3zx9zfUr
— Dark Web Informer (@DarkWebInformer) May 10, 2025
Who Was Behind This?
The operation was coordinated through Europol’s European Cybercrime Centre (EC3) and hosted at Europol’s headquarters in The Hague. The case was brought in the District of Utah, with the FBI’s Salt Lake City Field Office playing a lead domestic role alongside the Justice Department’s Computer Crime and Intellectual Property Section (CCIPS).
FBI Cyber Division Assistant Director Brett Leatherman stated that the agencies “seized users’ accounts, posts, credit details, private messages, and IP logs for evidentiary purposes,” adding that “no criminal is truly anonymous online.”
Europol’s EC3 Head Edvardas Šileris was equally direct, noting that the operation demonstrated no corner of the internet is beyond the reach of international law enforcement — and that what began as a shadowy forum for stolen data has now been dismantled.
The international partner list on the seizure banner is notable for its breadth: Romania’s DIICOT, Poland’s CBZC, the UK’s National Crime Agency, Australia’s AFP, Portugal’s Polícia Judiciária, Belgium’s Federal Police, Spain’s Guardia Civil, and the Dutch Politie — among others. This wasn’t a bilateral cooperation; it was a coordinated multinational strike.
Why This Matters
LeakBase wasn’t a dark web hidden service that required special tools to access. It was open web, English-language, and indexed. That accessibility was a feature for criminals and a liability that law enforcement was ultimately able to exploit.
The seizure has significant implications beyond the forum itself. All forum content — including users’ accounts, posts, credit details, private messages, and IP logs — has been secured and preserved for evidentiary purposes. That’s a goldmine for investigators. Anyone who posted, transacted, or communicated on the platform has left a trail, and law enforcement has now made clear they intend to follow it.
The FBI is actively soliciting tips from anyone who interacted with LeakBase administrators or staff, directing individuals to contact [email protected].
The Broader Crackdown Continues
The LeakBase takedown is the latest in a sustained campaign by Western law enforcement to systematically dismantle the infrastructure of the data breach underground. Over the past two years, authorities have seized or disrupted RaidForums, Breached, Genesis Market, and several ransomware-adjacent leak sites. Each successive operation has demonstrated improving international coordination and an accelerating tempo of enforcement.
Since 2020, CCIPS has secured the conviction of over 180 cybercriminals and IP criminals, and court orders for the return of over $350 million in victim funds.
For defenders and security professionals, the takedown is a reminder that breach data circulating in these forums doesn’t disappear on its own — it accumulates, gets repackaged, and gets weaponized in credential stuffing attacks, account takeovers, and fraud campaigns for years after the original incident. The disruption of the distribution layer matters.
For the users who thought Eastern European forum culture and a .la domain offered some insulation from U.S. law enforcement? March 3 was a rude awakening.
Operação “LEAK”
A @PJudiciaria participou numa operação policial coordenada pela @Europol que culminou na apreensão da base de dados do LeakBase, um dos maiores fóruns online do mundo utilizado por cibercriminosos para comprar e vender dados roubados.#OpLeak pic.twitter.com/39LKbY6MoW
— Polícia Judiciária (@PJudiciaria) March 4, 2026
Operation Leak reinforces a straightforward message that law enforcement has been sending with increasing clarity: the underground marketplace for stolen data has no safe harbor, and the people operating and patronizing these platforms are not as anonymous as they believe.