When ShinyHunters discovered Google Cloud Platform credentials buried in stolen Salesforce data, they didn’t just find a way into Telus Digital — they found the keys to nearly one petabyte of data belonging to one of Canada’s largest technology companies and dozens of its corporate clients.
The breach of Telus Digital, confirmed on March 12, 2026, represents one of the largest data thefts ever recorded by volume. But the real story isn’t the size — it’s the method. A single set of credentials, stolen from a completely separate breach, cascaded through cloud systems to expose call records, source code, FBI background checks, AI training data, and voice recordings for at least 28 major companies.
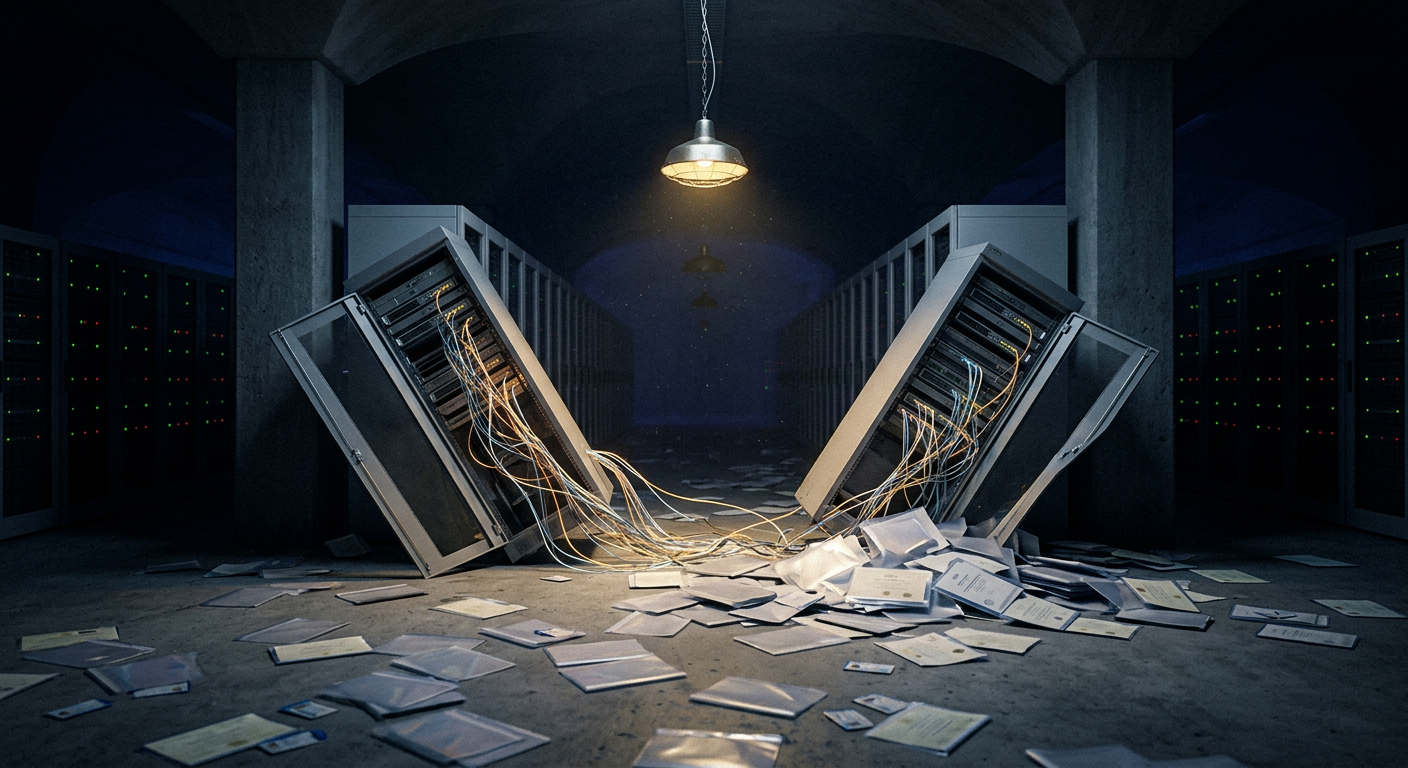
This is what supply chain compromise looks like in 2026. And it should terrify every CISO who outsources anything.
Who Is Telus Digital?
Telus Digital is the business process outsourcing (BPO) and digital services arm of Telus, Canada’s second-largest telecommunications provider. The company provides:
- Customer support outsourcing for major brands
- Content moderation for social media and tech platforms
- AI data services including training data labeling and annotation
- Fraud detection and prevention services
- Call center operations across multiple countries
Because BPO providers handle customer interactions for multiple companies simultaneously, they become single points of failure — one breach exposing dozens of clients’ data. This is exactly what happened.
The Attack Chain: From Drift to Disaster
Step 1: The Salesloft Drift Breach
The chain began with a breach of Salesloft’s Drift chat platform. In that incident, threat actors downloaded Salesforce data for 760 companies, including customer support tickets, internal communications, and system configurations.
Mandiant’s analysis confirmed that these support cases were systematically scanned for credentials, authentication tokens, API keys, and other secrets embedded in ticket data — the kind of sensitive information that helpdesk tickets routinely contain but organizations rarely think to protect.
Step 2: Credential Discovery
ShinyHunters found Google Cloud Platform (GCP) credentials for Telus Digital within the Drift data. These credentials — likely shared in a support ticket or internal communication — provided initial access to Telus’ cloud environment.
Step 3: Pivot and Expand
After accessing Telus’ GCP environment, ShinyHunters downloaded data from a large BigQuery instance. But they didn’t stop there. Using trufflehog — an open-source security tool designed to find secrets in code and data — they scanned the downloaded data for additional credentials.
This is a technique security professionals use in penetration testing: search through code repositories, configuration files, and data dumps for hardcoded passwords, API keys, and authentication tokens. ShinyHunters weaponized this defensive tool for offensive purposes, using each discovered credential to pivot into additional Telus systems.
Step 4: Multi-Month Exfiltration
According to BleepingComputer, the breach was first detected in January 2026, but Telus didn’t respond to media inquiries at that time. ShinyHunters had been inside the environment for months, methodically downloading data across multiple systems.
The multi-month dwell time allowed the threat actors to exfiltrate nearly 1 petabyte — roughly 1,000 terabytes — of data. To put that in perspective, that’s approximately:
- 500 billion pages of documents
- 250,000 hours of video
- The entire printed collection of the Library of Congress, roughly 200 times over
Reuters reported that ShinyHunters confirmed stealing at least 700 terabytes, while other claims put the figure closer to 1 petabyte.
What Was Stolen
The scope of stolen data is staggering:
Telus Digital BPO Data (28+ companies affected):
- Customer support interactions and call recordings
- Agent performance ratings and quality metrics
- AI-powered customer support tool data and training sets
- Fraud detection and prevention system data
- Content moderation workflows and decisions
Telus Telecommunications Data:
- Detailed call records (time, duration, originating number, destination number, quality metadata)
- Voice recordings of support calls
- Campaign and marketing data
- Consumer fixed-line business records
Corporate Data:
- Source code repositories
- FBI background checks on employees
- Financial information and internal documents
- Salesforce CRM data
The presence of FBI background checks is particularly alarming — this data includes highly sensitive personal information submitted for security clearances and employment verification.
The $65 Million Extortion
ShinyHunters reportedly demanded $65 million from Telus in exchange for not leaking the stolen data. Telus refused to negotiate, a decision that aligns with FBI and CISA guidance against paying ransoms but leaves the question of data exposure unresolved.
As of this writing, ShinyHunters has not released the full dataset, but the threat of publication creates ongoing risk for every company whose data was handled by Telus Digital’s BPO operations.
ShinyHunters: A Growing Threat
This isn’t ShinyHunters’ first massive breach. The group has built a reputation for large-scale data theft operations:
- 2020: Microsoft GitHub repositories, Wattpad (268M records), Mashable, Dave.com
- 2021: AT&T wireless customer data (70M records claimed)
- 2022: Operated BreachForums marketplace after RaidForums seizure
- 2024: Ticketmaster/Live Nation breach (560M records), Santander Bank (30M records)
- 2025: Salesloft Drift breach leading to 760 company data exposures
- 2026: Telus Digital (~1PB), Mercer Advisors breach
The group’s evolution from opportunistic data theft to sophisticated supply chain exploitation represents a maturation of criminal capabilities that rivals some state-sponsored operations.
The BPO Problem: Why This Keeps Happening
Telus Digital’s breach exposes a systemic vulnerability in how modern enterprises operate. The BPO industry — worth over $280 billion globally — creates massive concentrations of multi-client data in environments that individual clients have limited visibility into.
Consider the typical BPO relationship:
- Company A outsources customer support to a BPO provider
- BPO agents access Company A’s CRM, ticketing, and customer databases
- The BPO provider stores call recordings, chat logs, and support interactions
- Multiple companies’ data sits in the same BPO infrastructure
- Company A’s security team has no direct visibility into the BPO’s security posture
When the BPO is breached, every client is exposed simultaneously. And because BPO contracts often involve data from multiple business functions — support, billing, fraud, compliance — the breach touches every sensitive category at once.
Lessons for CISOs
1. Your Salesforce Tickets Contain Secrets
The initial attack vector — credentials found in Salesforce support tickets — is a problem hiding in plain sight at most organizations. How often do your employees paste API keys, passwords, or configuration details into support tickets? How often do vendors?
Action: Implement DLP scanning on your CRM and support ticket platforms. Search for patterns that match API keys, tokens, and credentials. Establish processes for sharing sensitive information that don’t involve pasting them into ticketing systems.
2. Audit Your BPO Providers
If you outsource any customer-facing operations, you need to know:
- What data does your BPO provider store?
- How long do they retain call recordings and chat logs?
- What cloud infrastructure hosts your data?
- What is their incident response plan, and will they notify you within your required timeline?
- Have they completed SOC 2 Type II and ISO 27001 audits?
Action: Request a data inventory from every BPO provider. Implement contractual requirements for security incident notification within 24 hours.
3. Credential Rotation After Upstream Breaches
The Drift breach happened before the Telus breach, but the stolen credentials were still valid. This suggests Telus either didn’t know their credentials were exposed or didn’t rotate them quickly enough.
Action: Monitor breach notification services for any mention of your organization. When an upstream vendor is breached, immediately rotate all credentials shared with or through that vendor — even if you’re not sure they were exposed.
4. Trufflehog Your Own Data
If ShinyHunters can use trufflehog to find credentials in your data, so can you. Run secret-scanning tools against your code repositories, cloud storage, databases, and data exports before an attacker does.
Action: Deploy secret scanning in CI/CD pipelines and conduct periodic scans of data stores for exposed credentials.
The Bigger Picture
The Telus Digital breach is a case study in how modern cyberattacks chain together. A breach at Salesloft exposed Salesforce data. That data contained GCP credentials. Those credentials opened Telus’ cloud environment. Trufflehog found more credentials. And a petabyte of data walked out the door over several months.
No single security failure caused this. It was a cascade of accumulated risk — credentials in tickets, insufficient monitoring, long dwell times, and the inherent concentration of data in BPO operations.
For CISOs, the lesson is clear: your security perimeter isn’t your network boundary. It’s the security posture of every vendor, partner, and service provider that touches your data. And right now, that perimeter has a ShinyHunters-shaped hole in it.